Successful implementation of an Information Security Management System (ISMS) requires clearly defined roles and responsibilities across the organization. This clarifies accountability, ensures management commitment, and helps maintain a robust security posture aligned with ISO/IEC 27001 requirements.
Key Roles and Their Responsibilities
Formalizing roles clarifies accountability and drives consistent ISMS execution. Here are the core roles typically involved in an organization’s information security management activities.
1. Top Management: The CEO, executives, and senior leaders plays a critical role in providing leadership, setting the tone, and allocating resources. They are responsible for:
Approving the ISMS policies, objectives, and scope
Ensuring sufficient resources and support for ISMS activities
Reviewing the ISMS performance periodically
Driving a culture that values information security
2. Information Security Manager: Also known as the ISMS Manager or Security Officer, this role oversees the day-to-day implementation and maintenance of the ISMS. Responsibilities include:
Developing and updating ISMS documentation and policies
Coordinating risk assessments and risk treatment plans
Managing controls and monitoring compliance
Reporting ISMS status to top management
3. Risk Owners: Risk Owners are individuals responsible for identifying, assessing, and managing risks related to their specific organizational areas. They:
Evaluate threats and vulnerabilities within their domain
Implement risk treatment actions
Monitor and report risk status
4. IT Manager/Security Officer: Focused on technical controls and IT infrastructure, this role manages:
Deployment and maintenance of security technologies
Conducting vulnerability assessments and penetration testing
Incident response and management
Monitoring security events and system integrity
5. Human Resources (HR): HR plays a vital part in information security through:
Conducting background checks and security clearances
Delivering security awareness and training programs
Enforcing access controls based on roles
6. Legal and Compliance Officer: Responsible for ensuring that the organization meets all legal and regulatory information security requirements. Duties include:
Monitoring changes in laws and regulations
Advising on compliance aspects and reporting obligations
Managing legal risks related to data breaches or incidents
7. All Employees: Every employee has a role to play in maintaining security by:
Following established security policies and procedures
Participating in security awareness training
Reporting security incidents or suspicious activities promptly
Formalizing Roles and Responsibilities
Documenting and Clarifying ISMS Roles and Responsibilities
ISO/IEC 27001 requires that information security roles and responsibilities be formally documented, communicated, and understood throughout the organization. Typical methods include:
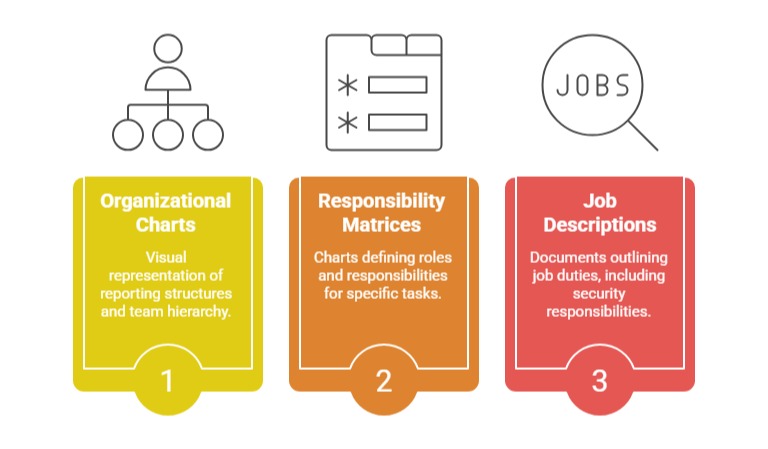
This clarity ensures that duties are assigned appropriately, segregation of duties is maintained, and continuous accountability is fostered.
Why are Defined Roles Critical?
| Reason | Description |
| Prevent Security Gaps and Overlaps | Clearly defined roles help avoid duplication of responsibilities and ensure no critical security tasks are overlooked. |
| Enable Effective Risk Management and Incident Handling | Assigned responsibilities ensure timely identification, assessment, and response to security risks and incidents. |
| Strengthen Organizational Commitment and Culture | Defined roles promote accountability and foster a strong information security culture across all levels. |
| Ensure Compliance with ISO/IEC 27001 Clause 5.2 | Role clarity supports adherence to ISO/IEC 27001 requirements for leadership, roles, and responsibilities in maintaining ISMS effectiveness. |
Ongoing Training and Awareness
Assigning roles is only effective when accompanied by suitable training and ongoing awareness programs to build the necessary competence and vigilance among personnel.
