Continuous improvement is a vital principle in managing and sustaining an effective Information Security Management System (ISMS) under ISO/IEC 27001.
Identifying opportunities for improvement enables organizations to enhance their security posture, adapt to evolving threats, and ensure compliance. It’s a proactive approach that drives the ISMS towards increasing maturity and resilience.
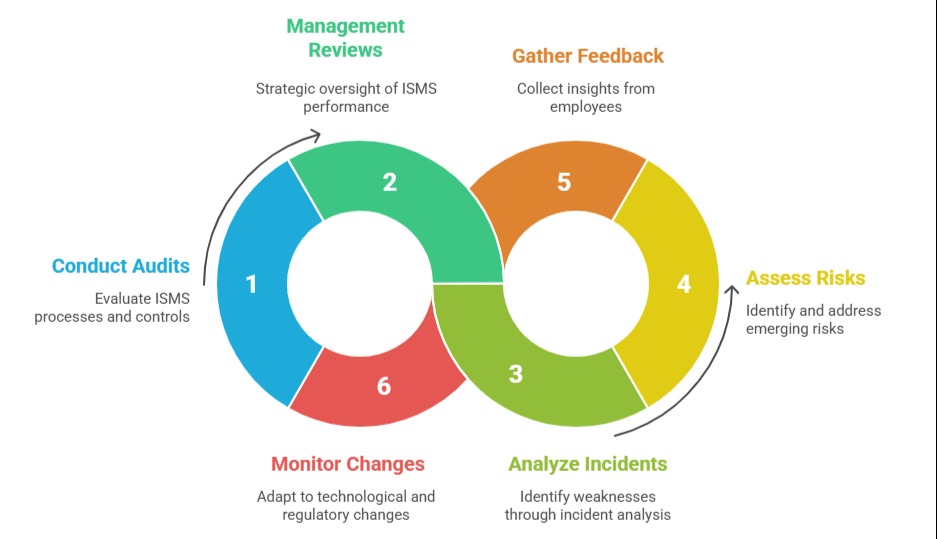
Sources of Improvement Opportunities
Continuous improvement depends on feedback and analysis from multiple organizational activities. Below are common sources that help uncover potential enhancements in the ISMS.
1. Internal and External Audits: Audits offer an independent assessment of the ISMS processes and controls. Audit findings often highlight nonconformities, inefficiencies, and potential gaps, serving as concrete indicators where enhancements are needed.
2. Management Reviews: Periodic management reviews provide a strategic oversight, evaluating performance data and trends in the ISMS. Discussions and decisions during these reviews may reveal areas needing adjustment or refinement based on business objectives and risk environment changes.
3. Incident and Event Analysis: Security incidents, failures, or near misses are valuable learning points. Root cause analysis of incidents uncovers fundamental weaknesses, leading to corrective actions and system improvements. Even minor incidents can reveal system vulnerabilities or process lapses.
4. Risk Assessments: Regular and updated risk assessments help identify emerging or previously overlooked risks. Addressing these risks through enhanced controls or revised processes presents agreed opportunities for improvement.
5. Employee Feedback and Suggestions: Staff involved in daily operations have firsthand experience and insights. Their feedback can identify cumbersome procedures, unclear policies, or new threats, contributing to practical improvements.
6. Technological and Regulatory Changes: Advances in technology or changes in regulatory requirements necessitate updates in the ISMS. Continuous scanning of these external changes ensures the organization adapts and remains compliant.
Embedding a Culture of Improvement
Organizations should foster an environment encouraging the identification of weaknesses and suggestions without fear. This involves leadership support, transparent communication channels, and rewarding proactive security behavior.
Documenting and Acting on Opportunities
Improvement opportunities should be formally recorded, prioritized, and integrated into the ISMS improvement plan. Follow-up actions, resource assignments, and timelines ensure implementations are tracked and verified for effectiveness.
Continuous Improvement Cycle
Identifying and acting on improvements aligns with the Plan-Do-Check-Act (PDCA) cycle, fundamental to ISO 27001. It ensures that learning from experience continually refines security management.