Preparing for an external certification audit is a critical phase in achieving ISO/IEC 27001 accreditation, which validates that your Information Security Management System (ISMS) complies with international standards.
This preparation involves thorough groundwork to demonstrate that your organization meets all mandatory requirements and maintains continuous control over its information security processes.
Understanding the Audit Stages
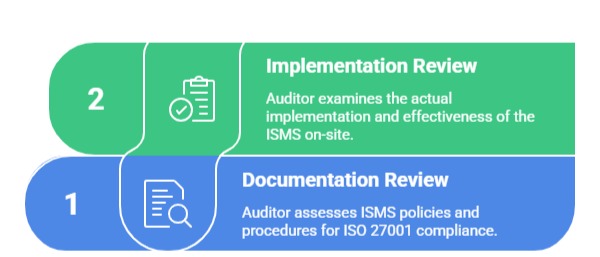
The external certification audit typically consists of two main stages:
Stage 1 Audit (Documentation Review): The auditor reviews your ISMS documentation, including policies, procedures, risk assessments, and the Statement of Applicability (SoA). This stage verifies whether your ISMS is designed according to ISO 27001 requirements and assesses your readiness for the full audit.
Stage 2 Audit (Implementation Review): This is a comprehensive on-site audit examining the actual implementation and effectiveness of your ISMS. Auditors will interview staff, inspect records, and test controls to ensure that documented processes are actively practiced and risks are managed effectively.
Key Preparation Steps
Readiness for audit requires attention to detail and active engagement across the organization. The list below highlights practical steps to prepare documentation, people, and processes.
1. Assemble and Review Documentation: Gather all mandatory and relevant documents such as the ISMS scope, policies, risk treatment plans, audit logs, training records, and corrective action reports. Conduct an internal review to identify and fix any inconsistencies or gaps in documentation.
2. Conduct Internal Audits: Perform a thorough internal audit to simulate the external audit experience. Address any nonconformities promptly and gather evidence demonstrating corrective actions. This exercise helps smooth the official audit process.
3. Train and Prepare Staff: Ensure that employees, especially those involved in the ISMS, understand their roles and can confidently answer auditor questions. Conduct awareness sessions highlighting audit objectives, the importance of compliance, and procedures.
4. Test Controls and Processes: Verify that security controls are functioning as intended through monitoring and testing procedures. Correct any deviations and document improvements thoroughly.
5. Address Risk Management: Review your risk assessment and treatment processes, ensuring risks are identified, prioritized, and mitigated appropriately. Ensure the Statement of Applicability clearly reflects control selection and their status.
6. Plan the Logistics: Coordinate with the external auditor to schedule the audit, provide access to facilities and systems, and prepare staff for interviews. Clear communication enhances audit efficiency.
Common Auditor Expectations
Auditors expect organizations to provide up-to-date records, leadership involvement, and proof of continual improvement. Below are standard expectations auditors use when assessing ISMS maturity.

Post-Audit Activities
After the audit, the certification body will provide an audit report highlighting findings. Any nonconformities must be addressed promptly with corrective action plans. Successful completion leads to certification issuance, which requires maintenance through surveillance audits.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.