ISO/IEC 27001:2022 is the globally recognized standard for an Information Security Management System (ISMS). Its purpose is to help organizations protect information assets by establishing a systematic approach to managing sensitive data.
This standard defines what an ISMS must include, how it should operate, and how to continually improve information security practices.
Scope of ISO/IEC 27001:2022
The scope of ISO/IEC 27001:2022 determines which parts of an organization and its information assets are covered by the ISMS. When defining scope, an organization considers:
1. The boundaries of the ISMS (e.g., entire organization, specific departments, locations)
2. Types of information and assets to be protected (e.g., digital records, physical documents, intellectual property)
3. Relevant regulatory, contractual, and business requirements (e.g., data privacy laws, customer contracts)
A clear and well-documented scope ensures that all stakeholders understand what the ISMS covers and avoids gaps in security controls.
Structure of ISO/IEC 27001:2022
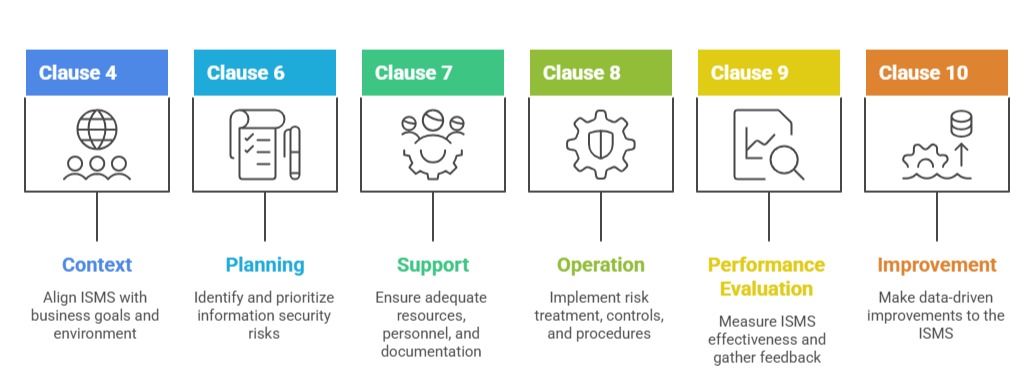
ISO/IEC 27001:2022 follows the High-Level Structure (HLS) used across all ISO management system standards. This shared structure makes it easier to integrate multiple management systems (e.g., quality, environment, continuity). The main clauses are:
Clause 1: Scope – Explains the purpose and applicability of the standard.
Clause 2: Normative References – Lists other standards referenced within ISO/IEC 27001.
Clause 3: Terms and Definitions – Defines key terminology used throughout the standard.
Clause 4: Context of the Organization – Requires understanding of internal and external issues, interested parties, and defining the ISMS scope.
Clause 5: Leadership – Specifies top management responsibilities, information security policy, and organizational roles.
Clause 6: Planning – Covers risk assessment, risk treatment, and setting information security objectives.
Clause 7: Support – Addresses resources, competence, awareness, communication, and documented information.
Clause 8: Operation – Focuses on implementing risk treatment plans, change management, and operational controls.
Clause 9: Performance Evaluation – Involves monitoring, measurement, analysis, evaluation, internal audit, and management review.
Clause 10: Improvement – Requires addressing nonconformities, corrective actions, and continual improvement.
Key Clauses and Their Importance
Annex A Controls
Annex A contains a catalog of 93 controls organized into four themes: organizational controls, people controls, physical controls, and technological controls.
These controls are optional measures selected based on the outcome of a risk assessment. They guide organizations in implementing specific safeguards, from access management and encryption to incident response and supplier relationships.
