Interviews are a key part of the audit process, providing valuable information that documents alone cannot reveal. Conducting effective interviews requires specific techniques to ensure accurate, detailed, and unbiased information collection.
These techniques help auditors build trust, encourage open dialogue, and gather evidence that reflects the true state of the Information Security Management System (ISMS).
Question Frameworks
Using a clear question framework allows auditors to structure interviews systematically, balancing between different types of questions:
1. Open-Ended Questions: Invite broad, descriptive answers that reveal detailed explanations or insights. For example, "Can you describe how user access is managed?"
2. Closed-Ended Questions: Require specific, often yes/no answers or factual data. For instance, "Do you have a documented access control policy?"
3. Probing Questions: Follow up on responses to clarify, explore further details, or uncover examples. For example, "Can you provide an example of how access rights are reviewed?"
A combination of these question types helps auditors navigate conversations thoughtfully and gather comprehensive evidence.
Active Listening
Active listening goes beyond simply hearing words; it involves fully focusing on the speaker, understanding the underlying message, and responding appropriately. Key elements include:
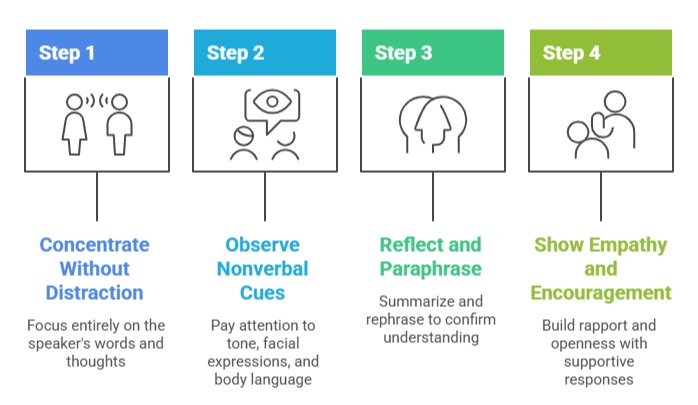
Active listening enables auditors to capture subtle details, detect inconsistencies, and create an atmosphere where interviewees feel comfortable sharing candidly.
Non-Leading Questions
Non-leading questions avoid suggesting an expected answer or influencing the interviewee’s response. They ensure objectivity and allow honest, unbiased information gathering. Examples include:
1. Instead of asking, "Do you always follow the incident response procedure?" ask, "Can you explain the steps you take when a security incident occurs?"
2. Rather than saying, "Isn’t it difficult to comply with the password policy?" say, "What challenges, if any, do you face with the password policy?"
Non-leading questions reduce the risk of skewed data, supporting evidence that fairly represents actual practices.
