An Information Security Management System (ISMS) audit is a systematic, independent review of an organization’s information security practices against ISO/IEC 27001:2022 requirements.
Audits play a critical role in organizational risk management by verifying that controls are implemented correctly, operate effectively, and address the risks identified during planning.
Purpose of ISMS Audits
The primary purpose of an ISMS audit is to provide assurance that information security controls meet defined requirements.
This involves checking whether policies, procedures, and technical safeguards align with the organization’s risk treatment plan and comply with ISO/IEC 27001 clauses.
Audits help organizations validate that controls are correctly selected based on risk assessments, effectively implemented, and maintained over time.
They also ensure transparency for stakeholders, such as customers, regulators, and partners—who rely on the organization’s information security posture.
Key Benefits for Risk Management
Effective risk management in an organization depends on how well potential threats are identified, evaluated, and controlled before they escalate.
ISMS audits play a crucial role by providing a structured and objective approach to uncover vulnerabilities, ensure compliance, and drive continuous improvement.
1. Early Identification of Vulnerabilities
Audits uncover gaps and weaknesses in controls before they lead to security incidents. By systematically reviewing processes, such as access management, encryption implementation, and incident response, auditors can detect potential vulnerabilities and recommend corrective actions.
2. Objective Evaluation of Control Effectiveness
Through evidence-based assessments, audits verify whether controls are functioning as intended. This objective evaluation builds confidence among management and stakeholders that the ISMS is reliable and resilient.
3. Continuous Improvement
ISMS audits generate formal findings, nonconformities, and observations that feed into corrective action processes. This feedback loop drives continual enhancement of policies, procedures, and technical safeguards, ensuring that the ISMS evolves in response to emerging threats and business changes.
4. Regulatory and Contractual Compliance
Many industries are subject to legal, regulatory, or contractual information security requirements. Regular audits demonstrate compliance with these obligations, reducing the risk of fines, legal disputes, and reputational damage.
5. Stakeholder Confidence and Trust
Sharing audit results, such as internal audit reports or certification audit outcomes—with customers and partners strengthens their trust in the organization’s ability to protect sensitive information. Third-party certification audits, in particular, provide independent validation of security practices.
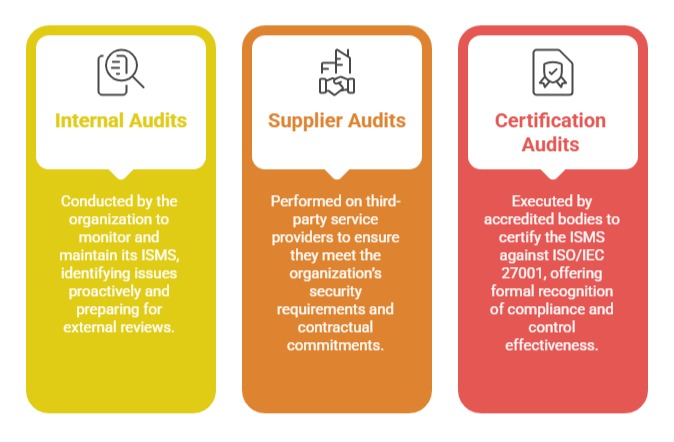
Audit Types and Their Role
Integrating Audits into Risk Management
Incorporating audit findings into the organization’s risk management cycle ensures that identified issues are treated as risks requiring action.
By linking audit outcomes to risk registers and treatment plans, organizations maintain a cohesive approach to identifying, assessing, and mitigating information security threats.
