In ISO/IEC 27001 audits, documentation serves as vital proof that an organization has implemented and operates its Information Security Management System (ISMS) effectively.
However, many organizations face challenges with incomplete, outdated, or inconsistent documentation, which can lead to audit nonconformities or delays.
Recognizing these issues helps organizations prepare better, improve their documentation quality, and increase audit success chances.
Common Documentation Gaps
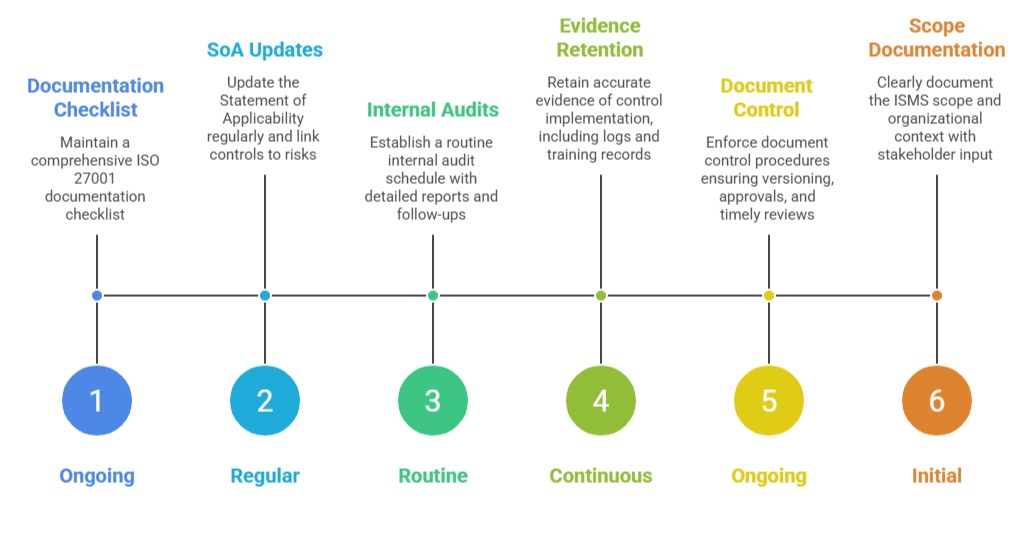
Following are the key areas where organizations often fall short in maintaining complete, accurate, and audit-ready ISMS documentation.
1. Missing Mandatory Documents
ISO 27001 requires several mandatory documents, including the information security policy, scope statement, Statement of Applicability (SoA), risk assessments, and treatment plans.
Missing any of these fundamental documents leads to significant audit findings because they are essential to demonstrate compliance and governance.
2. Incomplete or Outdated Statement of Applicability (SoA)
The SoA lists all Annex A controls and indicates which are applied or excluded, with justifications. Organizations often submit incomplete SoAs that do not explain exclusions or lack links between risks, controls, and documentation.
An outdated SoA not reflecting current ISMS status causes confusion and raises doubts on control effectiveness.
3. Weak Risk Assessment and Treatment Records
Organizations sometimes fail to provide detailed or up-to-date risk assessments. Risk treatment plans might be vague or missing responsibilities and timelines.
Without concrete evidence of risk management activities, auditors question the organization’s capability to handle information security risks properly.
4. Lack of Internal Audit and Management Review Records
Auditors expect documented evidence of scheduled and conducted internal audits along with management review minutes. Missing, incomplete, or superficial records on these activities signal poor ISMS oversight and are red flags during certification audits.
5. Inadequate Control Implementation Evidence
Even if policies and procedures exist, lack of proof that controls are actually applied is a common gap. Examples include missing access logs, incomplete training records, unrevised incident reports, or lacking backup and recovery test results.
Without evidence, auditors cannot confirm operational effectiveness.
6. Uncontrolled or Inconsistent Documents
Auditors look for version-controlled documents with review dates and approval records. Outdated policies, multiple conflicting document versions, or missing controls for document management may cause findings due to poor document governance.
7. Poorly Defined ISMS Scope or Context
Documentation that doesn’t clearly define the organization’s ISMS scope or context leads to ambiguity. This weakens risk identification efforts and may cause auditors to question the ISMS’s comprehensiveness.
How to Address These Gaps