Effective follow-up after an ISO/IEC 27001 audit is essential to ensure that identified nonconformities are properly resolved and that the Information Security Management System (ISMS) continually improves over time.
Tracking Action Closure
Once corrective actions are identified during an audit, they must be systematically tracked to completion.
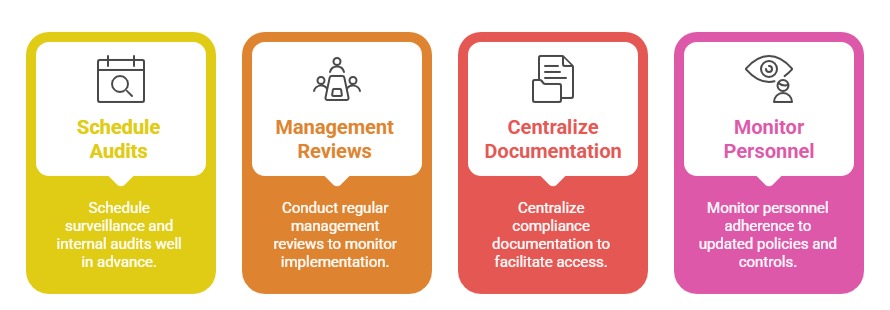
Establishing a centralized system or tool for logging corrective action requests (CARs), responsible owners, deadlines, and progress updates helps maintain visibility and accountability.
Regular progress reviews ensure that corrective measures do not stall and that resources are allocated appropriately.
Scheduling internal audits before surveillance audits creates an opportunity to verify that previous actions have been addressed satisfactorily.
Verifying Effectiveness of Corrections
Closed corrective actions need verification to ensure they have resolved the underlying issues and prevented recurrence.
Verification may include reviewing updated documentation, testing controls, performing repeat audits on affected processes, or interviewing personnel.
Evidence collected during verification should demonstrate that the corrective actions meet ISO/IEC 27001 requirements and that risks are effectively mitigated. This step is crucial to prevent superficial fixes that could leave vulnerabilities unaddressed.
Feedback Loop into Continual Improvement
ISO/IEC 27001 emphasizes continual improvement as a key principle. Results from corrective actions and audit findings should feed into the organization’s management reviews and risk assessments.
Discussing the status and outcomes of corrective actions provides senior management with assurance that the ISMS is evolving responsively to changing threats and organizational needs.
Additionally, applying lessons learned from past findings helps refine policies, processes, and controls, creating a proactive rather than reactive security culture.
Additional Best Practices