Two of the most important concepts that make configuration management reliable and scalable are automation and idempotency.
Automation replaces slow, error-prone manual processes with code-driven execution — ensuring tasks are performed consistently every time.
Idempotency ensures that no matter how many times an automated task runs, the result is always the same and no unintended changes are made.
Together, these two principles form the foundation of trustworthy configuration management.
Automation in Configuration Management
In a DevOps context, automation means defining tasks as code and letting tools execute them — consistently, at speed, and at any scale.
Rather than an engineer logging into each server and manually installing software or editing configuration files, automation handles all of it through a single command or pipeline trigger.
In configuration management, automation typically covers:
1. Installing and updating software packages across servers.
2. Managing configuration files and applying settings.
3. Starting, stopping, and restarting services.
4. Creating and managing user accounts and permissions.
5. Enforcing security policies and firewall rules.
The practical impact is significant. A task that might take an engineer several hours to perform manually across fifty servers can be completed in minutes through an Ansible playbook:
Automation also integrates directly into CI/CD pipelines, allowing configuration management to run automatically as part of every deployment, not just when someone remembers to do it manually.
What is Idempotency?
Idempotency is the property of an operation that ensures running it once or multiple times always produces the same end result — with no unintended side effects on subsequent runs.
In practical terms: if a task configures a server to have Nginx installed, an idempotent version of that task will install Nginx the first time it runs. If it runs again and Nginx is already installed, it does nothing — it does not reinstall, duplicate, or break anything.
Why idempotency matters in DevOps:
1. Safety: Automation can be re-run after a failure without causing double installations, duplicate entries, or broken configurations.
2. Predictability: The system always ends up in the same known state, regardless of its starting point.
3. Efficiency: Tasks that find the system already in the desired state are skipped, saving time and resources.
4. Confidence: Teams can run automation regularly — for compliance checks, drift correction, or scheduled enforcement — without fear of side effects.
A simple example illustrates the difference clearly. A non-idempotent shell script that appends a line to a file will add that line every time it runs, creating duplicates. An idempotent approach first checks whether the line already exists and only adds it if it does not.
How Ansible Implements Idempotency
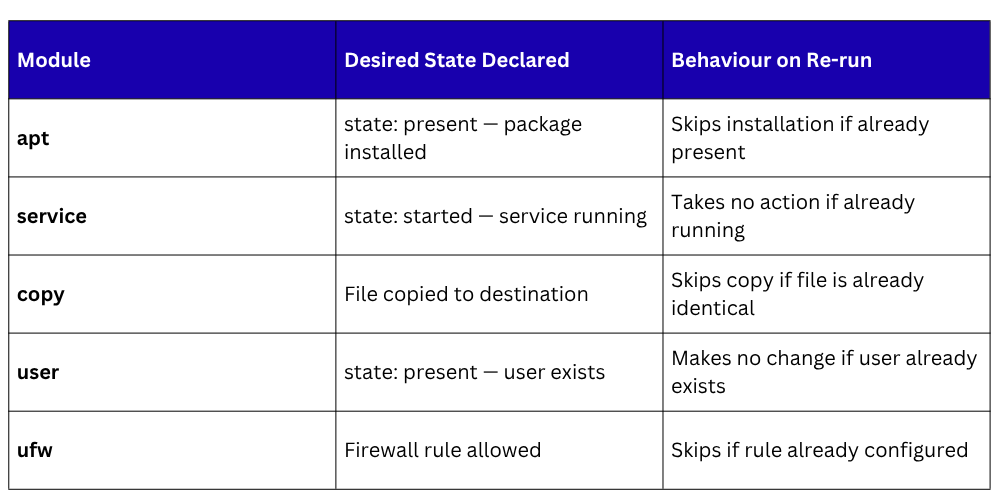
Ansible's modules are designed to be idempotent by default. Rather than executing commands blindly, each module checks the current state of the system before acting, and only makes a change if the current state does not match the desired state.
The engineer declares the desired end state, and Ansible handles the logic of whether any action is actually needed.
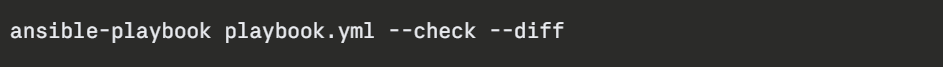
To verify idempotency before applying real changes, Ansible provides a dry-run mode:

Adding --diff shows exactly what would change, without making any changes:
Building Idempotent Playbooks
A well-written Ansible playbook is inherently idempotent, every task uses modules that check state before acting. Here is a practical example:
yaml
---
- name: Configure web server
hosts: webservers
become: true
tasks:
- name: Install Nginx
apt:
name: nginx
state: present
update_cache: yes
- name: Allow HTTP traffic through firewall
ufw:
rule: allow
port: '80'
proto: tcp
- name: Ensure Nginx is running and enabled
service:
name: nginx
state: started
enabled: true
On the first run, Ansible installs Nginx, configures the firewall rule, and starts the service. On every subsequent run, all three tasks report ok — meaning the desired state is already in place and no changes were made. This is idempotency working exactly as intended.
For situations requiring conditional logic, Ansible provides the register and when directives:
yaml
- name: Check if custom config exists
stat:
path: /etc/nginx/custom.conf
register: config_stat
- name: Copy config only if missing
copy:
src: custom.conf
dest: /etc/nginx/custom.conf
when: not config_stat.stat.exists
This pattern checks whether a file exists before attempting to copy it — skipping the task entirely if it is already in place.
Handlers — Triggered Automation Done Right
Handlers are a powerful Ansible feature that reinforces idempotency in a specific and important way. They run only when a task actually makes a change. This is particularly useful for restarting services after configuration changes.
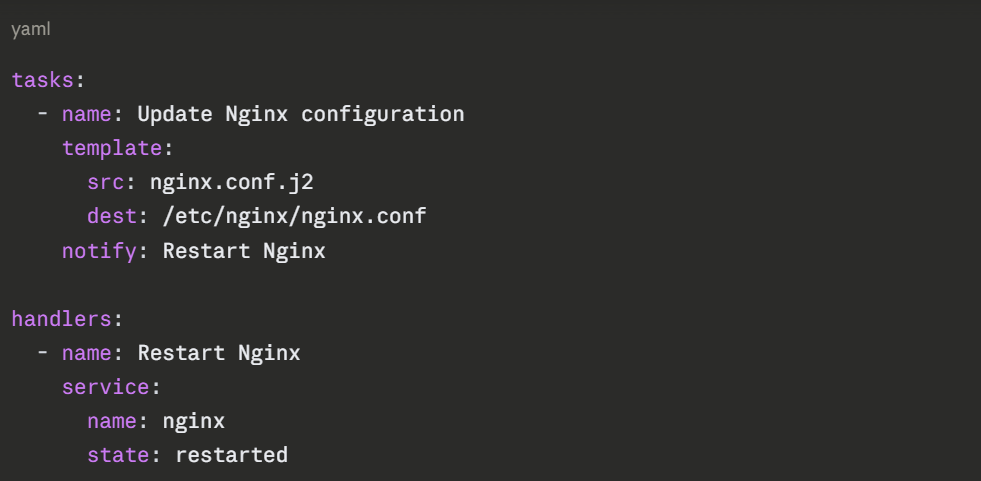
If the configuration file has not changed, the task reports ok, the handler is never notified, and Nginx is not restarted unnecessarily. If the file does change, the handler runs once at the end of the playbook.
This avoids unnecessary service restarts, a simple but impactful application of idempotency.
Automation and Idempotency in CI/CD Pipelines
When Ansible playbooks are integrated into a CI/CD pipeline, automation and idempotency work together to provide continuous configuration enforcement, ensuring servers are always in their defined state, not just when someone manually runs a playbook.
A GitHub Actions workflow step running an Ansible playbook looks like this:

Because the playbook is idempotent, this step can run on every pipeline execution, even if the configuration has not changed. Servers that are already correctly configured are unaffected. Servers that have drifted from their desired state are automatically corrected.
Common Pitfalls to Avoid
1. Using the command or shell module carelessly: These modules run raw commands that are not inherently idempotent. Always prefer purpose-built modules where available, and add appropriate guards when shell commands are unavoidable.
2. Writing custom scripts outside Ansible: External scripts bypass Ansible's idempotency guarantees entirely.
3. Hardcoding values: Use variables instead of hardcoded values to keep playbooks reusable and environment-agnostic.
4. Skipping the --check flag during development: Always validate playbook behavior with a dry run before applying to production systems.
