Core threats such as those outlined in the OWASP Top 10 represent the most common and impactful security risks facing modern web applications.
These threats include weaknesses in application design, implementation, and configuration that attackers can exploit.
Common attack vectors like injection and cross-site scripting target how applications handle user input and execute code, often leading to data breaches, unauthorized access, or service disruption.
OWASP Top 10 Overview
The OWASP Top 10 represents the Open Web Application Security Project's consensus on the most critical web application security risks, updated periodically based on global data from vulnerabilities and incidents.
It serves as an industry standard for prioritizing security efforts, helping developers focus on high-impact areas without overwhelming detail.
Each category includes common attack vectors, exploitation techniques, and prevention strategies tailored for modern web apps.
This list evolves with threats; the 2021 version emphasized shifts like consolidating cross-site scripting (XSS) under injections, while recent drafts highlight emerging issues like supply chain risks.
Injection Attacks
Injection flaws occur when untrusted data is sent to an interpreter as part of a command or query, allowing attackers to manipulate the intended logic.
These are among the oldest and most destructive threats, often leading to unauthorized data access or full system takeover. In the OWASP Top 10 2021, injections rank as A03:2021 – Injection, covering SQL, NoSQL, command, and more.
Common Injection Vectors
Attackers exploit inputs like form fields, URLs, or APIs without proper sanitization. Here's a breakdown:
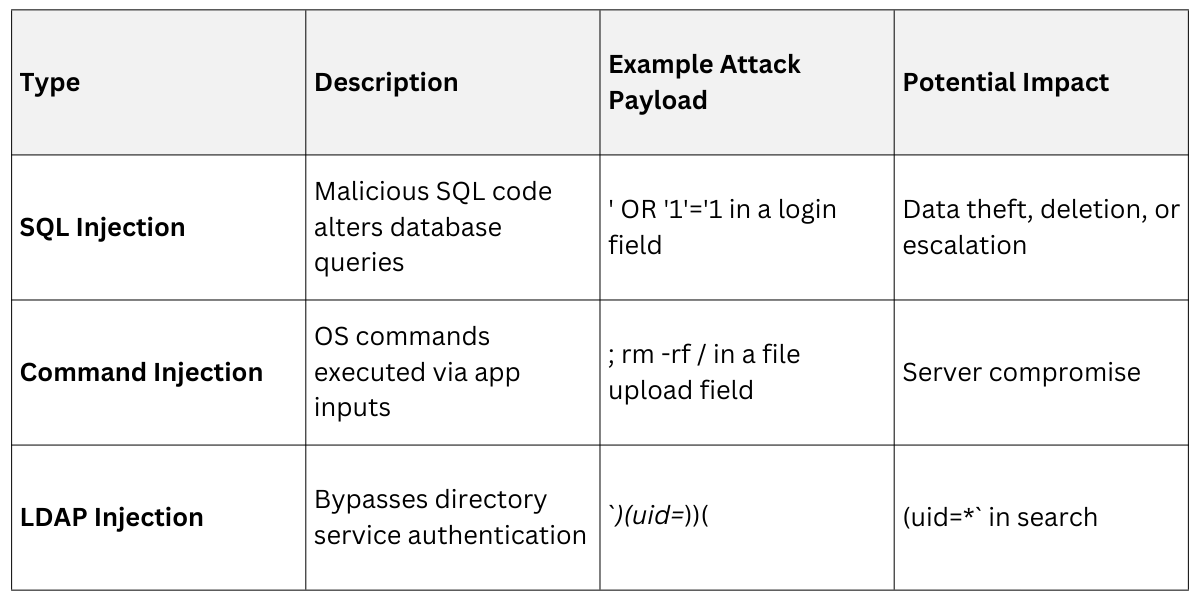
Real-World Example: An e-commerce site's search bar accepts user input directly into a SQL query, letting attackers dump customer records.
Prevention Steps
Follow these numbered practices to block injections:
1. Use prepared statements and parameterized queries (e.g., PDO in PHP, psycopg2 in Python) to separate code from data.
2. Apply input validation with allowlists for expected formats (e.g., reject non-numeric IDs).
3. Employ web application firewalls (WAFs) like ModSecurity for runtime detection.
4. Store database credentials securely and least-privilege principles.
Cross-Site Scripting (XSS)
XSS happens when attackers inject malicious scripts into web pages viewed by other users, exploiting trust in the site. Now folded into injection risks in recent OWASP lists, it remains a top vector due to its prevalence in dynamic content.
These attacks steal cookies, session tokens, or keystrokes, often evading detection in client-side code.
Types of XSS
.png)
Example: A forum post with <script>alert('Hacked!');</script> executes for every reader if not escaped.
Mitigation Techniques
1. Output encoding: Escape data based on context (HTML, JS, URL) using libraries like OWASP ESAPI or DOMPurify.
2. Content Security Policy (CSP) headers restrict script sources: Content-Security-Policy: script-src 'self'.
3. Validate inputs: strictly and avoid eval() or innerHTML for user data.
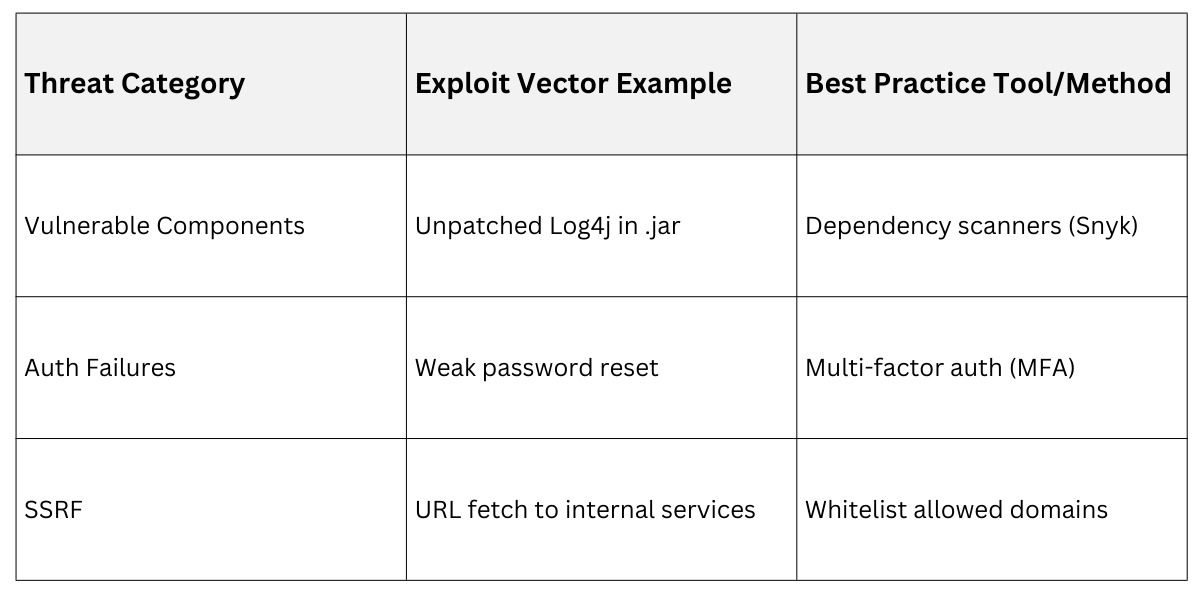
Other Key OWASP Threats
Beyond injections and XSS, the Top 10 covers diverse vectors requiring layered defenses. Broken Access Control (A01:2021) tops recent lists, where users access unauthorized functions via URL tweaks or privilege escalation.
Access Control Breakdown
Attackers force browse to hidden paths or elevate roles. Prevention:
1. Enforce role-based access control (RBAC) server-side.
2. Validate objects (e.g., check user owns resource ID).
3. Use secure session management without exposed tokens.
Cryptographic Failures (A02:2021) expose sensitive data via weak encryption or leaks in transit/logs. Mitigate with TLS 1.3, strong hashing (Argon2), and key rotation.
Security Checklist
1. Automate secure configs with tools like Ansible.
2. Remove debug info in production.
3. Apply least-privilege to cloud/IaaS.
 Integrating Defenses in Development
Integrating Defenses in Development
Secure coding starts in the SDLC. Use threat modeling to map risks early, then automate scans with tools like OWASP ZAP or Burp Suite. For Python/Flask apps (common in your web dev work), integrate Flask-Talisman for headers and SQLAlchemy for safe queries.
Practical Exercise: Audit a sample login form for injection/XSS by fuzzing inputs with payloads from OWASP's cheat sheets.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
