Authentication and authorization design patterns define how systems verify user identities and control access to resources in a secure and scalable way.
Authentication focuses on confirming who a user or service is, while authorization determines what actions or resources that identity is allowed to access. Well-designed patterns help enforce security policies consistently across applications, services, and APIs.
Authentication Patterns
Authentication verifies user identities using credentials or tokens, a critical first layer in app security. Modern patterns shift from basic passwords to resilient, user-friendly methods compliant with NIST and OWASP guidelines.
Password-Based Authentication
Traditional yet evolved, this pattern hashes passwords with algorithms like bcrypt or Argon2, enforcing minimum lengths of 8-15 characters based on MFA usage.
Salts prevent rainbow table attacks, and strength meters guide users during registration. Always transmit over TLS to avoid interception.
1. Block common breached passwords via services like Pwned Passwords.
2. Implement login throttling: lock accounts after 5-10 failed attempts within an observation window, using exponential backoff.
3. Use constant-time comparison functions to thwart timing attacks.
For recovery, send generic messages like "If the email exists, check your inbox" to prevent enumeration.
Multi-Factor Authentication (MFA)
MFA adds layers like OTPs, biometrics, or hardware tokens, blocking 99.9% of compromises per Microsoft analysis. Deploy adaptively: require it for sensitive actions or new devices.
Implementation steps
-Picsart-CropImage.png)
In banking apps, MFA prevents unauthorized transfers even if credentials leak.
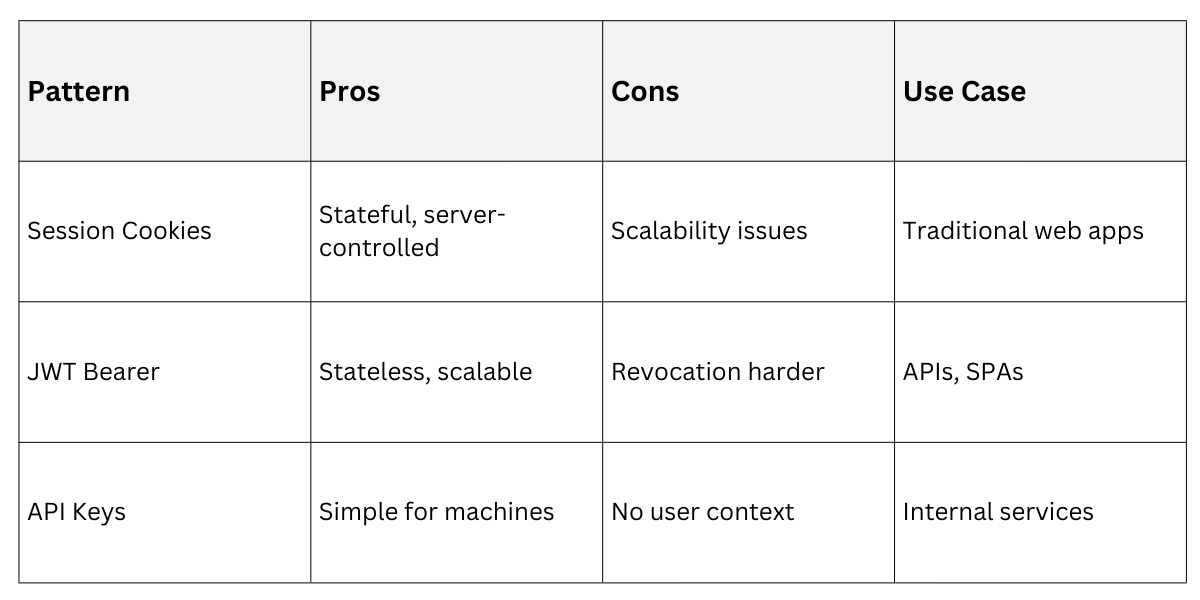
Token-Based Authentication
JWTs (JSON Web Tokens) enable stateless sessions: sign payloads with user claims, validate signatures server-side. Pair with short expirations and refresh tokens stored securely.
OWASP recommends validating issuer, audience, and expiration on every request.
Federated and Passwordless
OAuth 2.0/OIDC delegates to providers like Google, using ID Tokens for identity. Passwordless trends use FIDO2/WebAuthn passkeys for phishing-resistant biometrics.
1. OAuth Flow: Authorization code grant with PKCE for public clients.
2. Zero Trust Integration: Verify device posture continuously.
Enterprise apps favor SAML for SSO across domains
Authorization Patterns
Authorization decides what authenticated users can do, enforcing least privilege via deny-by-default rules. Patterns scale from monoliths to microservices, aligning with Zero Trust.
Role-Based Access Control (RBAC)
RBAC assigns permissions to roles like "admin" or "user," simplifying audits in stable hierarchies. Finance apps use it for compliance.
Strengths and Limits
1. Fast lookups, easy onboarding.
2. Role explosion in complex apps.
Check roles per request: if (user.hasRole("admin")) allowDelete();.
Attribute-Based Access Control (ABAC)
ABAC evaluates policies on user attributes (role, location), resources, and environment (time, IP). NIST SP 800-162 endorses it for granularity.
Example Policy: Allow access if user.department == resource.owner && time < 18:00.

Advanced Patterns
ReBAC grants based on relationships, e.g., "edit if owner" in social apps. Microservices use gateway token propagation or centralized policy services like Cerbos.
1. Edge authenticates, issues JWT with claims.
2. Services verify and enforce locally or query PDP.
3. Log decisions for audits.
Zero Trust mandates continuous verification, no implicit trust.
Best Practices and Implementation
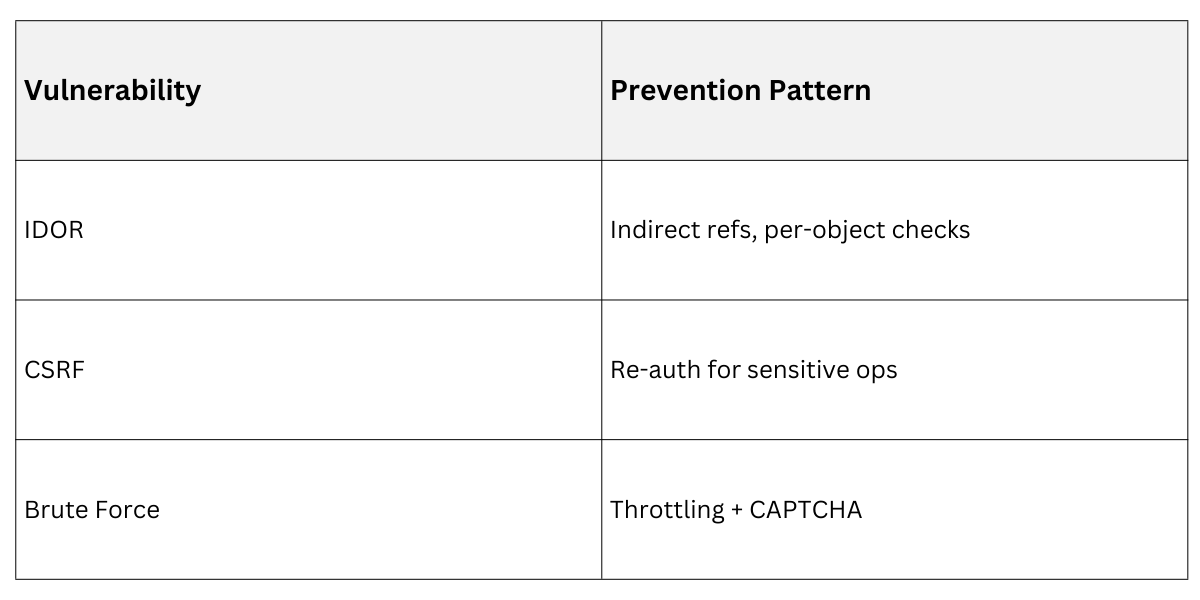
Secure designs integrate patterns holistically, avoiding client-side checks.
1. Session Management: Server-side stores, sliding expiries, regenerate IDs post-login.
2. Error Handling: Generic responses ("Invalid credentials") prevent enumeration.
3. Logging: Track failures, lockouts; centralize in SIEM.
4. Testing: Unit test edge cases, like IDOR via indirect references.
In a Python FastAPI app, use Depends(OAuth2PasswordBearer) for tokens, then ABAC middleware.
Common Pitfalls and Trends
Avoid "forgot one check" by centralizing enforcement in filters/middleware. 2026 trends emphasize machine auth for AI agents via MCP/OAuth profiles.
Pitfalls: Role creep, missing static resource checks (e.g., S3 buckets).
Trends: Passkeys dominate, AI-driven adaptive auth.
Regular audits prevent privilege escalation.
