Software Composition Analysis focuses on identifying and managing the risks associated with third-party and open-source dependencies used in software projects.
Modern applications rely heavily on external libraries, which can introduce security vulnerabilities, licensing issues, and supply chain risks.
SCA tools analyze dependency inventories to detect known vulnerabilities and help teams maintain secure and compliant software.
What is SCA?
SCA automates the detection, analysis, and management of open-source and third-party components in software projects.
It scans dependencies against vulnerability databases, license inventories, and quality metrics to uncover hidden risks.
Modern applications depend heavily on libraries like Log4j or npm packages, creating complex supply chains vulnerable to attacks.
SCA provides visibility into direct and transitive dependencies—those pulled in indirectly by primary ones.
Key Elements
1. Vulnerability scanning for CVEs from sources like the National Vulnerability Database (NVD).
2. License compliance checks for terms like GPL or MIT to avoid legal issues.
3. Software Bill of Materials (SBOM) generation for a complete inventory of components.
4. Dependency health assessment, flagging outdated or unmaintained libraries.
Why SCA Matters in AppSec
SCA addresses the explosion of third-party code, reducing supply chain attack risks that surged 300% recently. It aligns with OWASP guidelines for early integration in DevSecOps to prevent vulnerable libraries from reaching production.
In application security, SCA complements custom code scanning by targeting external risks organizations often overlook. For instance, the Log4Shell flaw in Apache Log4j affected countless apps because teams lacked dependency visibility—SCA flags such issues proactively.
Benefits
1. Risk reduction: Prioritizes high-severity CVEs with exploit details and patches.
2. Compliance: Meets mandates like U.S. Executive Order 14028 requiring SBOMs.
3. Efficiency: Automates manual reviews, cutting detection time from months to minutes.
SCA vs Other Scanning Tools
SCA differs from tools like SAST, which analyze custom code logic, by focusing on third-party risks.

Using both in CI/CD pipelines eliminates blind spots across the full stack. DAST tests runtime behavior, while SCA handles static dependency analysis.
How SCA Works
SCA follows a structured process to scan and report on dependencies. Tools parse project files and cross-reference against databases for comprehensive coverage.
-Picsart-CropImage.png)
Example: In a Node.js project, SCA detects an outdated lodash version with a prototype pollution CVE, recommending an upgrade.
Implementing SCA: Step-by-Step
Integrate SCA early via "shift-left" practices for maximum impact. OWASP recommends placing it before SAST/DAST in pipelines.
Follow these steps
1. Select a tool: supporting your languages (e.g., Java, Python, JS).
2. Integrate into CI/CD: Add as a GitHub Action or Jenkins plugin for automated scans on pull requests.
3. Set policies: Define thresholds (e.g., block high-CVSS vulns) and license allowlists.
4. Remediate: Auto-update deps where safe; manually review reachability.
5. Monitor continuously: Rescan for emerging threats and generate audit reports.
Best Practices
1. Start small with one repo, scale organization-wide.
2. Train teams on false positives to build trust.
3. Combine with SBOM tools for regulatory compliance.
Popular SCA Tools Comparison
Choose tools based on needs like language support or CI/CD fit. Top 2026 options include open-source and commercial solutions.
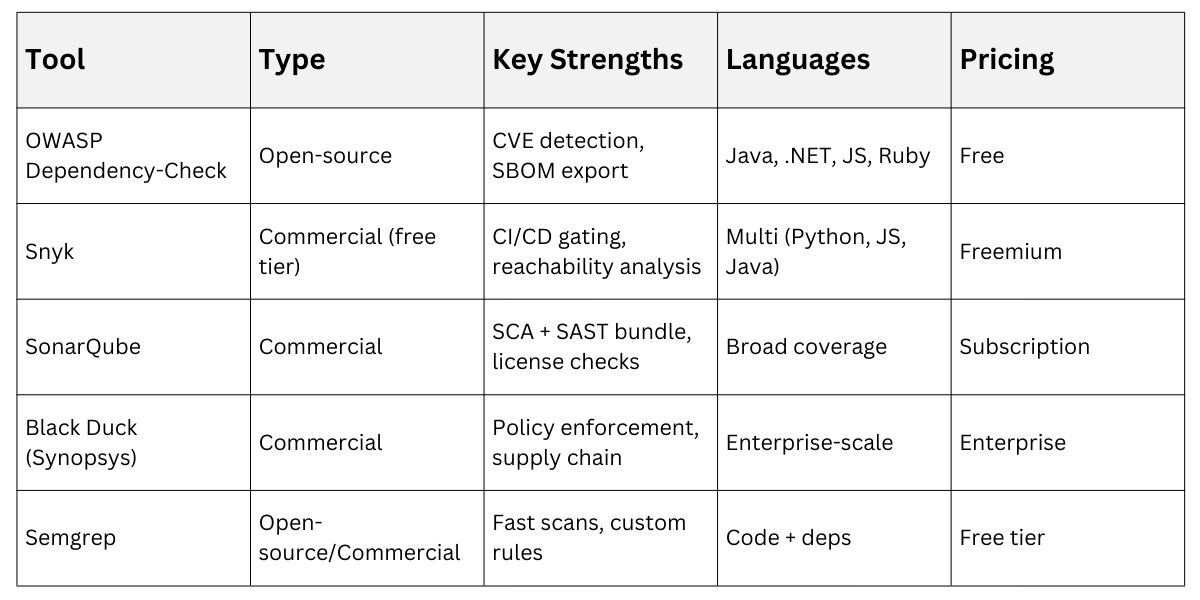
For Python devs, Safety CLI checks pip deps quickly.
Challenges and Best Practices
Common hurdles include false positives and legacy app support. Address by tuning policies and phasing in scans.
-Picsart-CropImage.png)
SCA streamlines compliance with GDPR/HIPAA via automated reports.
