Runtime Application Self-Protection mechanisms are security techniques that protect applications from attacks while they are running.
RASP operates from within the application, monitoring execution flow and user behavior to detect malicious activity in real time.
By responding immediately to threats, RASP helps prevent exploitation of vulnerabilities without relying solely on external security controls.
What is RASP?
RASP operates as an embedded security layer within software applications, monitoring runtime behavior to detect and block attacks dynamically.
Unlike network-level defenses, it uses deep contextual awareness of the application's code, data flows, and execution paths.
Key Characteristics
.png)
Consider a web app handling user logins; RASP could flag anomalous SQL queries formed from tainted inputs, preventing exploitation before database impact.
How RASP Works
RASP leverages instrumentation techniques to gain visibility into application execution, combining this with threat intelligence for precise decisions. Deployment typically occurs during development or via runtime agents, ensuring seamless integration.
The Core Process
1. Instrumentation Phase: Embed sensors into the codebase using techniques like binary instrumentation or JVM hooks. These monitor API calls, memory access, and control flows.
2. Runtime Monitoring: Collect data on application state, user inputs, and execution paths, building a baseline of normal behavior.
3. Threat Detection: Analyze anomalies using rules, machine learning models, or behavioral signatures—e.g., detecting SQL injection by validating query construction.
4. Response Actions: Block malicious flows, log events, or alert security teams, often with options for passive monitoring in production.
5. Feedback Loop: Update rules based on detected threats, enhancing accuracy over time.
This inline approach provides zero-day protection since decisions rely on application-specific context, not just network patterns.
RASP vs. Traditional Security Tools
RASP complements rather than replaces perimeter defenses, offering superior accuracy due to its application-level insight. Perimeter tools like Web Application Firewalls (WAF) inspect traffic blindly, leading to higher false positives.
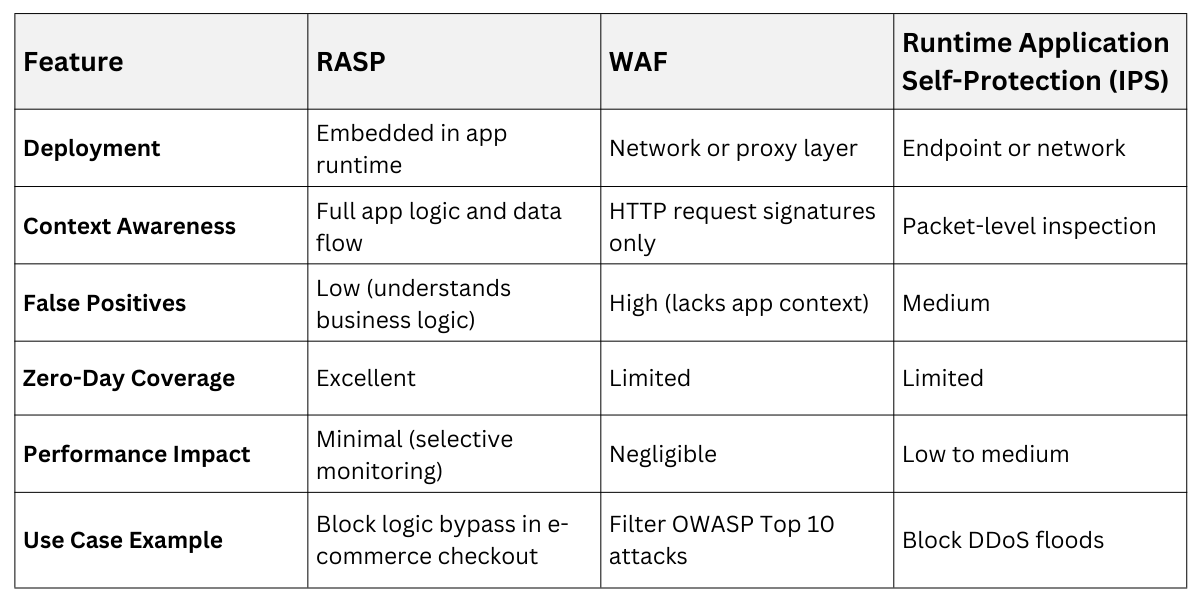
RASP shines in microservices where WAFs struggle with encrypted internal traffic, as seen in cloud environments.
Key Benefits and Use Cases
RASP delivers tangible advantages in accuracy, agility, and compliance, making it ideal for DevSecOps pipelines. It reduces alert fatigue by filtering noise through contextual analysis.
1. Reduced False Positives: Deep visibility distinguishes benign inputs from attacks—e.g., a legitimate URL parameter mimicking XSS won't trigger blocks.
2. Zero-Day and Logic Attack Defense: Catches exploits without signatures, like business logic flaws in authentication flows.
3. Compliance Support: Aligns with standards like OWASP Top 10 and PCI-DSS by logging precise attack attempts for audits.
4. Developer-Friendly: Integrates into CI/CD, providing runtime feedback during testing.
Practical Use Cases
1. Protecting APIs in fintech apps from injection and deserialization attacks.
2. Securing mobile backends against reverse engineering tampering.
3. Safeguarding serverless functions from runtime exploits in AWS Lambda.
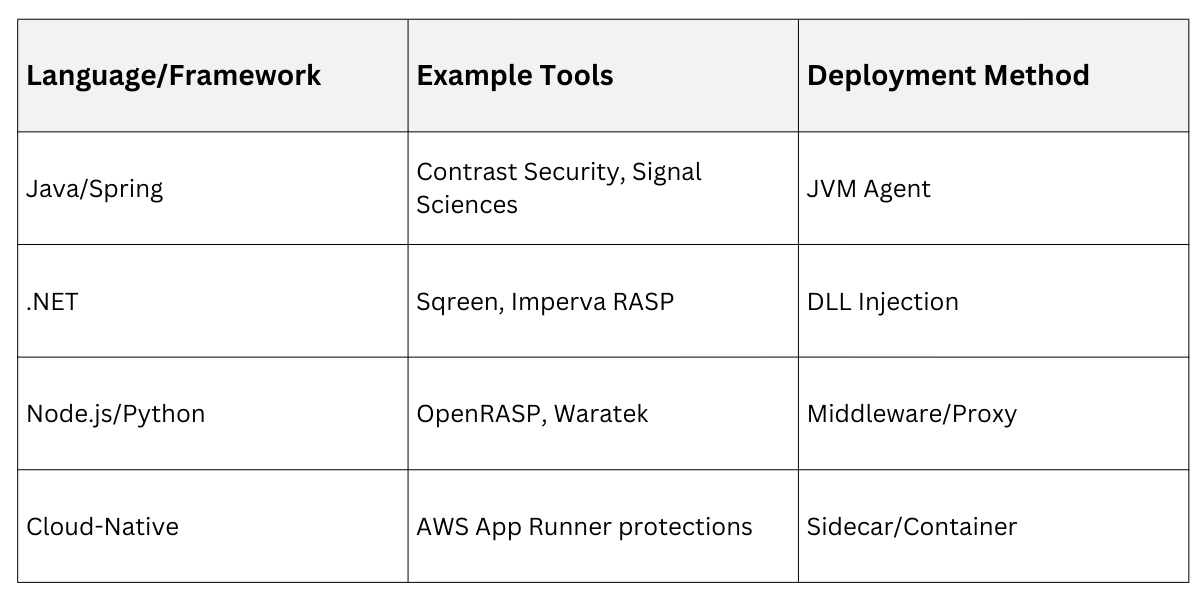
Implementation Approaches
RASP solutions vary by language and architecture, with commercial and open-source options available. Choose based on app stack—e.g., Java agents for enterprise or lightweight libraries for Python/ Node.js.
Common Techniques
1. Binary Instrumentation: Modifies executable code at runtime (e.g., via libraries like Pin or Valgrind).
2. Library Interception: Replaces standard libs (e.g., JVM agent hooking Java calls).
3. Source Code Integration: Embed via SDKs during build, minimizing overhead.
Best Practice: Start in learning mode to baseline traffic, then enable blocking. Test thoroughly to avoid performance regressions under load.
Challenges and Best Practices
While powerful, RASP introduces overhead and requires tuning to avoid disrupting legitimate traffic. Common pitfalls include over-instrumentation slowing apps or misconfigurations exposing gaps.
Mitigation Strategies
-Picsart-CropImage.png)
In production, monitor metrics like latency and block rates; tools like Contrast provide dashboards for this. For compliance-heavy sectors, ensure RASP logs support GDPR or SOC 2 requirements.
Real-World Examples
Leading vendors demonstrate RASP's evolution. Contrast Security's Protect agents scan for OWASP risks inline, blocking 99% of attacks with sub-millisecond latency. Imperva RASP uses AI to model normal flows, auto-tuning for custom apps.
In a 2025 breach report, RASP adopters saw 40% fewer exploits in runtime compared to WAF-only setups, highlighting its edge in API-heavy ecosystems.
RASP equips applications with self-awareness, dramatically lowering exploit success rates through precise, context-rich defenses. Integrate it early in your security posture for resilient, autonomous protection that scales with modern development.
