Session management and secure data storage best practices are critical for protecting user information and maintaining application security.
Effective session management ensures that user sessions are created, maintained, and terminated securely, preventing threats such as session hijacking or fixation.
Secure data storage focuses on protecting sensitive information at rest through techniques like encryption, access control, and proper key management.
Session Management Fundamentals
Sessions track user interactions across requests in stateless protocols like HTTP. Effective session management prevents attackers from impersonating users by stealing or guessing session identifiers.
Start with secure token generation and lifecycle handling to establish a strong baseline. This ensures sessions remain confidential, tamper-proof, and short-lived.
Sessions typically use cookies or tokens (e.g., JWTs) to maintain state. Always generate unique, unpredictable session IDs with at least 128 bits of entropy—random strings like a1b2c3d4e5f67890 won't cut it against brute-force attacks.
Key Principles of Secure Sessions
Follow these OWASP-recommended guidelines to harden sessions:
Use HTTPS exclusively: Encrypt all traffic to protect session data in transit (TLS 1.3+ mandatory in 2026).
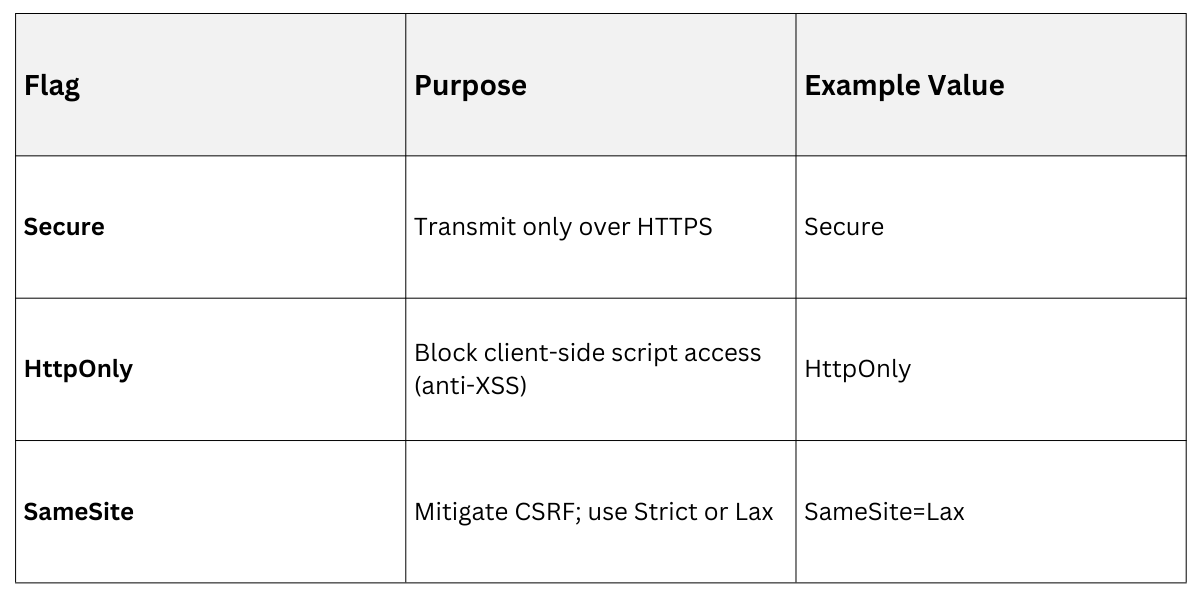
Set secure cookie flags
Regenerate IDs on privilege changes: After login or role elevation, issue a new ID to invalidate any stolen ones.
Practical Example: In a Python Flask app, set cookies like response.set_cookie('session_id', value, secure=True, httponly=True, samesite='Lax').
Session Lifecycle Best Practices
Manage sessions from creation to destruction with these steps:
.png)
Tie sessions to user agents or IPs loosely (allow for proxies) to detect anomalies.
Advanced Session Security Techniques
Beyond basics, modern apps face sophisticated threats like token replay or side-channel attacks. Advanced techniques layer defenses using standards like OAuth 2.1 and mutual TLS.
Implement these to future-proof your apps against evolving threats. They integrate seamlessly with frameworks like Django or Spring Security.
Token-Based Sessions (JWTs and Beyond)
JSON Web Tokens (JWTs) store state client-side but require strict handling. Use signed and encrypted JWTs (JWE) over plain HS256.
Pros and Cons at a Glance
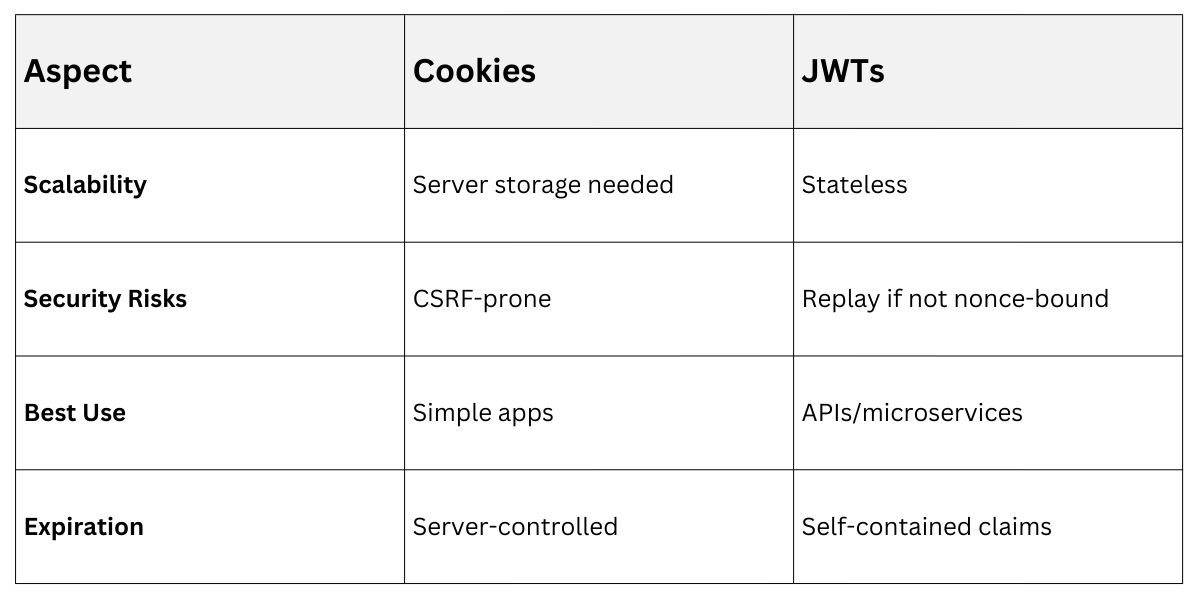
Mitigate JWT Pitfalls
1. Bind to jti (unique ID) and validate nonce/state parameters.
2. Shorten expiration (e.g., 15 minutes) with refresh tokens stored securely.
3. Example claim: {"sub": "user123", "exp": 1699999999, "aud": "yourapp.com"}.
Detecting and Responding to Session Attacks
Monitor for anomalies like rapid ID guesses or geographic jumps.
1. Rate limiting: Cap login/session attempts at 5/hour per IP.
2. Behavioral analysis: Flag logins from new devices; prompt MFA.
3. Logging: Record session events without PII (GDPR-compliant).
n code, use libraries like python-jose for JWTs: validate with jwt.decode(token, key, algorithms=['ES256']).
Secure Data Storage Strategies
Once sessions authenticate users, apps store data like profiles or carts—often sensitive. Secure storage ensures data remains confidential even if disks are compromised.
1. Focus on encryption, access controls, and auditing to protect at rest and in use. This aligns with PCI-DSS and HIPAA for regulated apps.
2. Data classification drives choices: public (no encryption), private (encrypted), secret (key-managed).
Encryption Best Practices
Encrypt at rest using AES-256-GCM; derive keys with PBKDF2 or Argon2 (OWASP Cheat Sheet).
1. Key management: Use Hardware Security Modules (HSMs) or services like AWS KMS—never hardcode keys.
2. Field-level encryption: Encrypt specifics like SSNs, not whole DBs, for efficiency.
3. Envelope encryption: Wrap data keys with a master key.
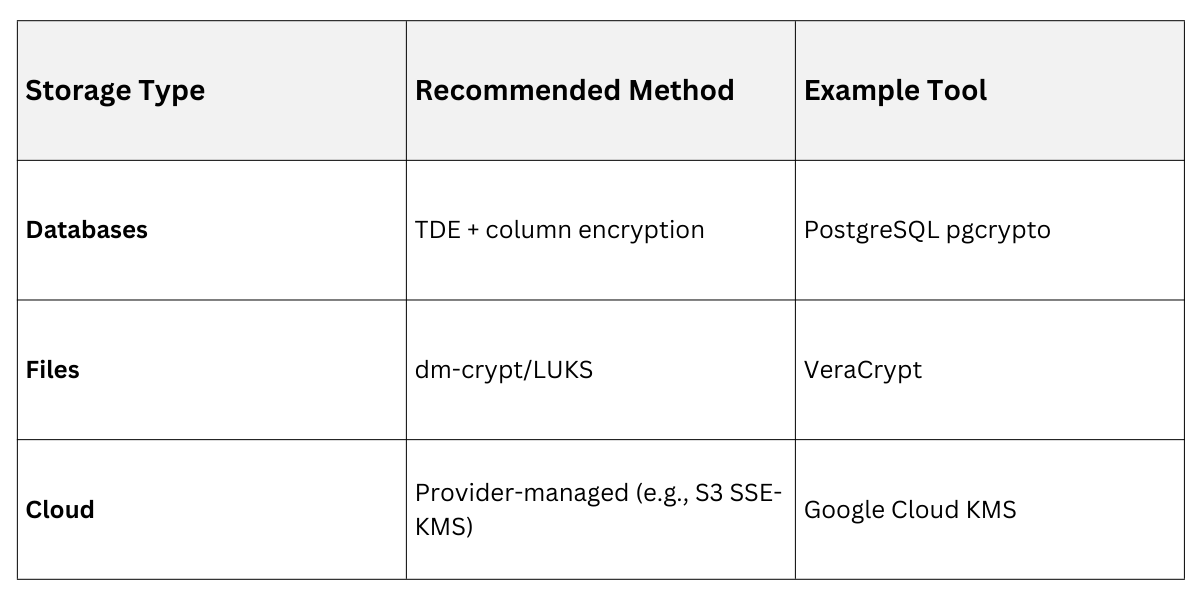
Example: In SQL, INSERT INTO users (email_enc) VALUES (AES_ENCRYPT('user@example.com', key));.
Access Controls and Least Privilege
Enforce RBAC/ABAC to limit exposure.
1. Row-level security: Queries filter by user ID automatically.
2. Secrets management: Store API keys in HashiCorp Vault or Azure Key Vault, not env vars.
3. Immutable storage: Use append-only logs for audits.
Practical Tip: For web apps, hash passwords with bcrypt/scrypt (cost 12+); verify with checkpw(hash, password).
Common Pitfalls and Defenses
Avoid these traps
-Picsart-CropImage.png)
Integrating Sessions and Storage in Real Apps
Tie it together in full-stack apps. Holistic integration ensures sessions control storage access securely.
Use sessions to gate data fetches. Example: Middleware checks session.user_id before DB queries.
Monolithic vs. Microservices
1. Monolith: Shared session store (Redis cluster).
2. Microservices: Propagate via headers (e.g., Authorization: Bearer <JWT>), validate per service.
Audit Trail: Log access with WHO/DID_WHAT/WHEN format, anonymize where possible.
