Interactive Application Security Testing and runtime protection focus on identifying and mitigating security vulnerabilities while an application is running.
IAST combines elements of static and dynamic testing by monitoring application behavior from within during execution, providing accurate insights into vulnerabilities and their root causes.
Runtime protection mechanisms observe application activity in real time and can detect or block malicious behavior as it occurs.
What is Interactive Application Security Testing (IAST)?
IAST represents a hybrid evolution in app security testing, combining the precision of static analysis with the realism of dynamic testing.
It instruments your running application to monitor code execution, data flows, and interactions without needing separate scans.
Unlike older methods, IAST provides context-aware results by observing how data moves through your app in real time. This makes it ideal for modern CI/CD pipelines where speed and accuracy matter.
Core Principles of IAST
IAST works by injecting lightweight agents into your application runtime, such as JVM for Java apps or Node.js processes.
These agents track taint analysis—tracing untrusted user input from entry points like HTTP requests to sensitive sinks like database queries.
1. Real-time monitoring: Captures vulnerabilities during actual app usage, reducing false positives common in scans.
2. Contextual awareness: Understands business logic, spotting issues like insecure deserialization that static tools miss.
3. Low overhead: Modern IAST tools add under 2-5% CPU usage, per benchmarks from Contrast Security (2024 reports).
For example, imagine a Python Flask app handling user logins. IAST would flag if input from a form taints a SQL query, showing the exact code path—far more actionable than a generic alert.
How IAST Differs from Other Testing Methods
To grasp IAST's value, compare it with peers. It shines in interactive scenarios, like developer testing or staging environments.
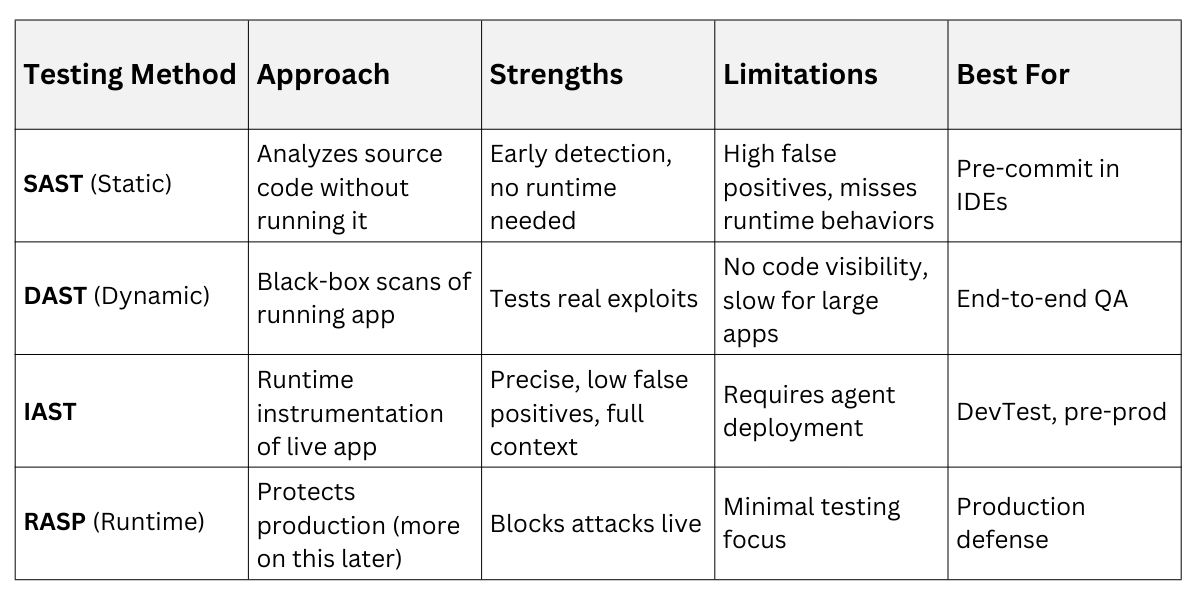
This table highlights why IAST bridges the gap—it's proactive during development, aligning with DevSecOps best practices from Gartner (2025).
How IAST Works in Practice
Deploying IAST involves simple integration steps that fit seamlessly into your workflow. Agents hook into the app's runtime, analyzing execution flows without altering code.
Start with popular tools like Contrast Security, Synopsys Seeker, or open-source options like AppSealing. They support languages from Java and .NET to Python and Node.js.
Step-by-Step IAST Implementation
Follow this numbered process to set up IAST in a sample Node.js app:
-Picsart-CropImage.png)
In a real e-commerce app, IAST might detect a Server-Side Request Forgery (SSRF) when user-supplied URLs hit internal services, providing a stack trace and exploit payload for quick patching.
Benefits and Real-World Use Cases
IAST accelerates secure development by cutting remediation time by up to 80%, according to 2024 Veracode State of Software Security report.
1. Shift-left security: Developers spot issues locally, before code review.
2. Compliance aid: Maps to standards like PCI-DSS 4.0 and GDPR with audit-ready reports.
3. Cloud-native fit: Scales for Kubernetes via sidecar agents.
Consider a fintech firm: IAST caught zero-day Log4Shell variants in runtime, preventing data leaks during Black Friday traffic spikes.
Runtime Protection: From Detection to Defense
Runtime protection evolves IAST into active defense via Runtime Application Self-Protection (RASP). While IAST observes, RASP blocks exploits in production, embedding security directly in the app.
This duo ensures your app not only tests securely but stays resilient against evolving threats like AI-generated attacks.
Key Features of RASP
RASP agents use the same instrumentation as IAST but add enforcement layers. Latest features (2025 updates) include ML-driven anomaly detection.
1. Attack blocking: Auto-quarantines sessions on threats like XSS, with customizable policies.
2. Behavioral analysis: Learns normal traffic, flagging outliers (e.g., sudden API spikes).
3. Transparent deployment: No network proxies; works inline with minimal latency (<1ms).
4. Forensics logging: Captures full attack context for post-incident review.
Tools like Imperva RASP or Signal Sciences (Fastly) lead here, with open-source alternatives like Traefik plugins.
Integrating IAST and RASP for Full Lifecycle Security
Combine them for end-to-end coverage: Use IAST in dev/test, flip to RASP in prod.
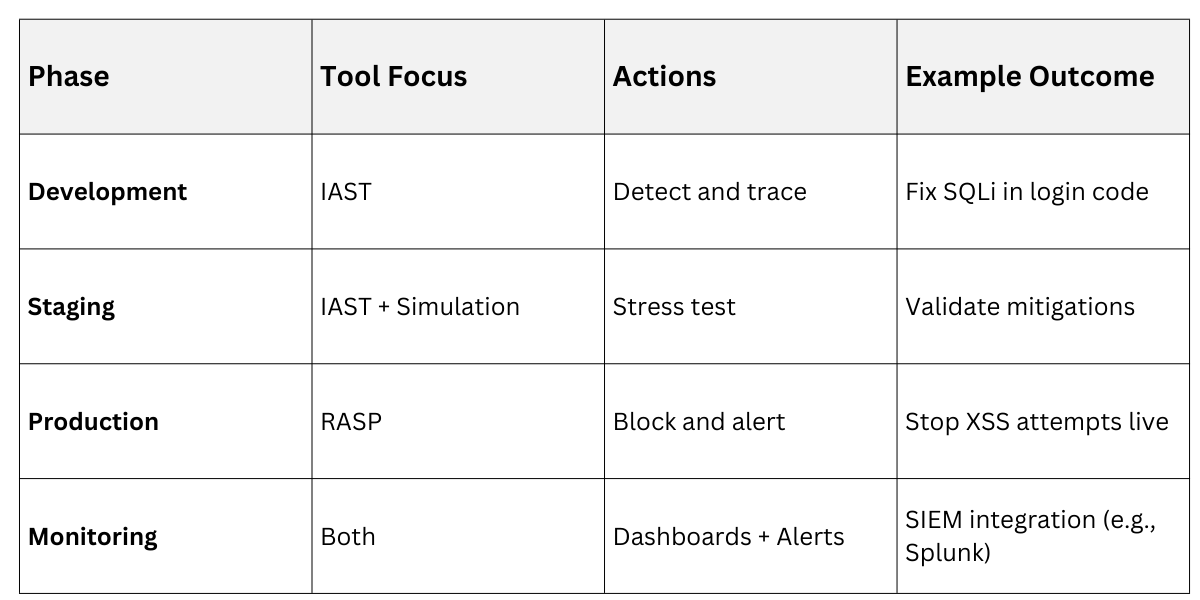
A banking app example: IAST identifies weak JWT validation pre-launch; RASP blocks tampered tokens in prod, logging for SOC teams.
Best Practices and Limitations
Adopt these for success:
-Picsart-CropImage.png)
Limitations include language support gaps (e.g., less mature for Go) and potential for agent crashes—mitigate with canary deployments.
