Incident response planning for application breaches involves preparing processes and procedures to detect, contain, and recover from security incidents.
A well-defined plan helps teams respond quickly and effectively when an application is compromised, minimizing damage, downtime, and data loss.
It also ensures clear communication, role assignment, and compliance with legal and regulatory requirements during an incident.
Why Incident Response Planning Matters?
Every application breach starts small but escalates fast without a plan—think unauthorized access snowballing into data exfiltration.
A solid plan turns panic into process, aligning with frameworks like NIST Cybersecurity Framework (CSF), which emphasizes Identify, Protect, Detect, Respond, and Recover pillars. Without it, teams improvise, prolonging exposure and amplifying harm.
Breaches hit hard: the average cost reached $4.88 million in 2024 per IBM's Cost of a Data Breach Report, up 10% from prior years. Poor response accounts for 30-40% of that tally.
Key Drivers
-Picsart-CropImage.png)
Practical Example: In the 2024 Twilio breach, pre-existing response plans limited damage to scoped API endpoints, unlike reactive firms facing weeks of cleanup.
Key Components of an Incident Response Plan
An effective plan is a living document outlining roles, tools, and triggers—customized to your app's stack, like web apps with microservices or mobile backends. It evolves with threats, tested quarterly via simulations.
Core elements ensure coordinated action, reducing mean time to respond (MTTR) from days to hours.
.png)
Tailor to your environment: for a Python/Flask app, include database snapshots and container isolation scripts.
The Incident Response Lifecycle
Follow a structured lifecycle to handle breaches methodically—NIST SP 800-61r2's gold standard, updated for cloud-native apps. This phases approach prevents oversight, with each step building on the last.
It starts with preparation and loops back post-recovery, fostering continuous improvement.
1. Preparation: Build and train on the plan
Inventory assets (e.g., APIs, user DBs).
Run tabletop exercises simulating an XSS breach.
2. Identification: Detect and classify the incident
Monitor via logs, IDS/IPS alerts.
Triage: Is it a breach? (e.g., unusual API traffic spikes).
3. Containment: Isolate without destroying evidence
Short-term: Rotate credentials, firewall rules.
Long-term: Segment networks, deploy WAF blocks.
4. Eradication: Remove root cause
Scan for malware, patch vulnerabilities (e.g., CVE-2024-1234 in your auth library).
Validate with vulnerability scanners like Nessus.
5. Recovery: Restore operations securely
Roll back from clean backups.
Monitor for re-infection 48-72 hours post-recovery.
6. Lessons Learned: Document and update
Conduct PIR within 7 days.
Share anonymized insights across teams.
Practical Example: During the 2023 LastPass breach, swift containment (step 3) via vault isolation prevented broader vault compromises, though eradication revealed deeper persistence.
Building Your Incident Response Plan Step-by-Step
Crafting a plan from scratch feels daunting, but break it into actionable steps tailored for application teams. Start small, iterate with feedback from devs and ops.
This process ensures buy-in and realism, incorporating tools like runbooks in Git for version control.
1. Assemble the Team: Include devs, security, legal, execs
Define RACI matrix (Responsible, Accountable, Consulted, Informed).
2. Conduct Risk Assessment: Map app threats
Use STRIDE model: Spoofing, Tampering, etc.
Prioritize high-impact paths like payment APIs.
3. Define Triggers and Playbooks: Scenario-specific guides
Breach types: DDoS, injection, insider threats.
4. Select and Integrate Tools
Logging: Centralized with Fluentd.
Alerting: PagerDuty for on-call rotations.
Forensics: Volatility for memory dumps.
5. Test and Train: Simulate quarterly
Red team exercises mimicking real breaches.
6. Document and Distribute: Store in accessible repo (e.g., Confluence)
Review annually or post-major update.
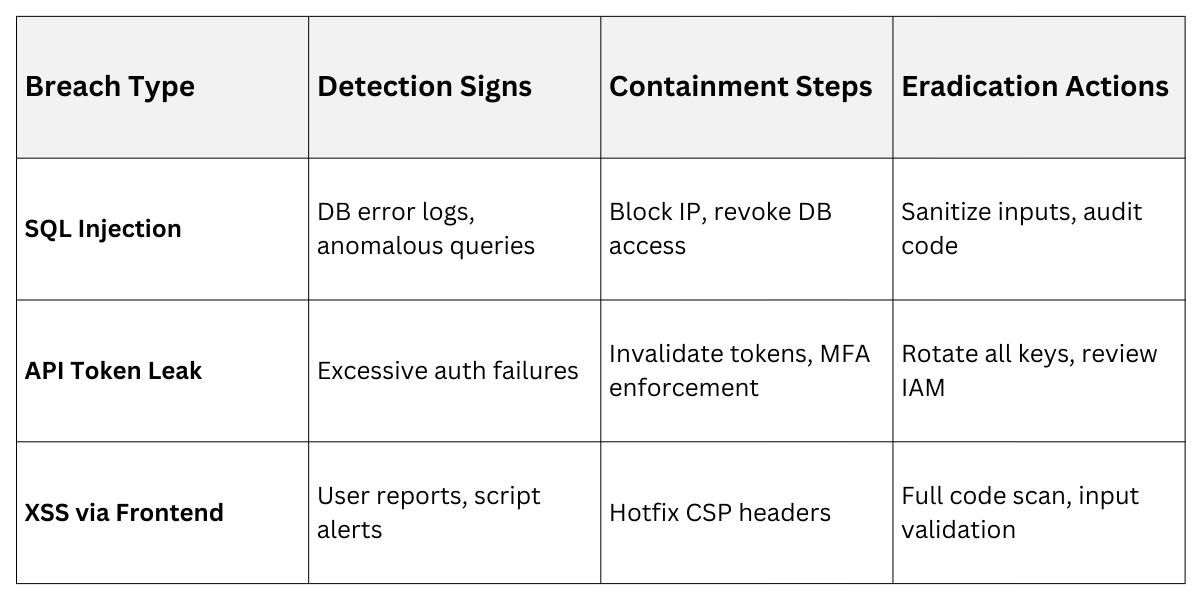
Common App Breaches
Real-world Tip: Etsy’s 2016 breach playbooks cut response time by 50% through pre-built scripts.
Legal and Compliance Considerations
Breaches trigger legal duties—notify users, regulators within mandated timelines. For apps handling PII, non-compliance invites penalties up to 4% of global revenue under GDPR.
Integrate these from day one to avoid scramble.
1. Notification Rules: 72 hours (GDPR/EU), 6 hours critical infra (India CERT-In).
2. Evidence Preservation: Chain-of-custody for forensics, avoiding spoliation.
3. Vendor Management: SLAs for third-party breaches (e.g., cloud providers).
4. Insurance Alignment: Cyber policies require documented response.
Example: The 2024 AT&T breach led to $5M+ fines partly due to delayed SEC disclosures—highlighting exec reporting needs.
Testing, Training, and Continuous Improvement
Plans decay without practice; treat them as code—test, deploy, refactor. Annual audits and post-breach PIRs keep them sharp amid threats like zero-days.
Embed culture: Gamify drills with leaderboards for engagement.
-Picsart-CropImage.png)
