Error handling and logging without information leakage focus on managing application failures in a secure and controlled manner.
Proper error handling ensures that exceptions are caught and handled gracefully, providing users with meaningful but non-sensitive feedback.
Secure logging captures sufficient diagnostic information for developers and operators while avoiding the exposure of sensitive data such as credentials, internal system details, or stack traces.
Why Error Handling and Logging Matter in Secure Apps
Error handling ensures your app fails gracefully under stress, while logging captures events for auditing without handing attackers a roadmap. Together, they prevent information disclosure—a top risk where debug output reveals internals like file paths or user data.
The Risks of Poor Error Practices
Attackers probe apps with malformed inputs to trigger errors, hoping for leaks. Verbose errors amplify this: a stack trace might spill server details, encryption keys, or query structures, enabling targeted attacks.
Consider a simple SQL injection attempt. Without proper handling, the database error "Table 'users' does not exist" reveals your schema.
Industry data from Verizon's 2024 DBIR shows 74% of breaches involve human error, often tied to leaky logs.
Key Risks
1. Stack trace exposure: Reveals code paths, frameworks, and versions (e.g., "Django 4.2.7").
2. Sensitive data in logs: User PII, tokens, or credentials logged accidentally.
3. Denial-of-service amplification: Custom errors that crash under load.
 Core Principles of Secure Error Handling
Core Principles of Secure Error Handling
Principle 1: Always distinguish between development and production environments—debug mode on production is a red flag. Principle 2: User-facing errors should be generic; internals stay hidden.
In practice, map exceptions to safe responses. For instance, in Python Flask
try:
user = fetch_user(input_id)
except DatabaseError:
# Log internally, return generic error
logger.error("DB fetch failed for ID: %s", input_id, exc_info=True)
return {"error": "Service unavailable"}, 503This logs the exception with context but shows users only "Service unavailable."
Implementing Safe Exception Handling
Follow these steps to harden your code:
-Picsart-CropImage.png)
Best Practices
1. Enable only in dev: app.config['DEBUG'] = False.
2. Use middleware: Centralize handling (e.g., Express.js errorHandler).
3. Test with fuzzing: Tools like OWASP ZAP simulate bad inputs.
Best Practices for Secure Logging
Logging is your app's black box recorder—vital for forensics but dangerous if mishandled. Aim for structured logging (JSON format per RFC 5424) to parse easily without leaks.
Structured Logging Without Leaks
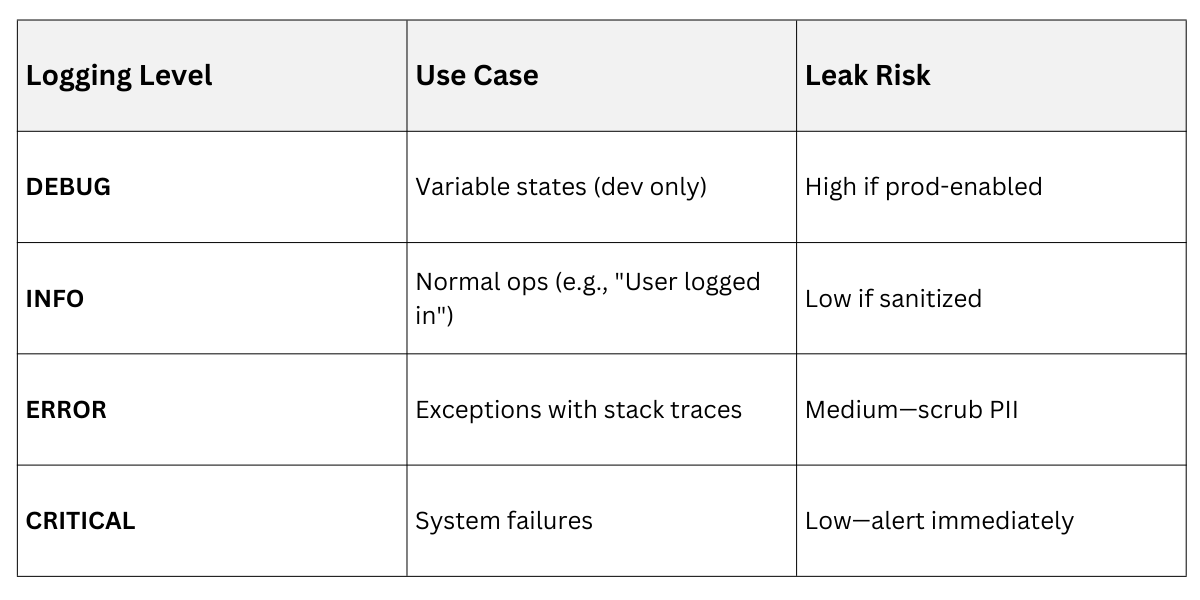
Start every log with severity levels: DEBUG, INFO, WARN, ERROR. Tools like Python's logging module or Winston (Node.js) support this natively.
Sanitize inputs before logging—never raw user data. Use levels wisely: DEBUG for dev, ERROR for alerts.
Example configuration in Python
import logging
import json
from logging.handlers import RotatingFileHandler
logger = logging.getLogger('app')
handler = RotatingFileHandler('app.log', maxBytes=10**6)
formatter = logging.Formatter('{"time": "%(asctime)s", "level": "%(levelname)s", "msg": "%(message)s"}')
handler.setFormatter(formatter)
logger.addHandler(handler)Process for Safe Entries
1. Capture context: Add correlation IDs (e.g., UUID per request).
2. Sanitize payloads: Replace secrets with [REDACTED]; use libraries like python-logging-redact.
3. Avoid concatenation: Use parameterized logging: logger.error("Failed for user_id=%s", user_id) not f"Failed for {user.email}".
4. Rotate and secure files: Limit size, encrypt at rest (e.g., AWS CloudTrail).
5. Centralize: Ship to ELK Stack or Splunk for analysis.
Real-World Example: During a 2024 Log4Shell variant attack, apps with sanitized logs detected anomalies via ERROR spikes without exposing JVM details.
Common Pitfalls and How to Avoid Them
Even experts slip—here's how to sidestep traps. A classic: Logging full HTTP requests, leaking auth headers.
Pitfall 1: Verbose User Errors
Problem: Default frameworks dump stacks (e.g., Rails' rescue_from without config).
Fix:
1. Custom error pages: Static HTML for 404/500.
2. Middleware override: Intercept and rewrite.
Pitfall 2: Third-Party Leaks
Libraries like Sentry or DataDog can leak if misconfigured. Fix: Whitelist fields; use filters.
 Integrating with Monitoring and Compliance
Integrating with Monitoring and Compliance
Tie errors/logs to tools like Prometheus for metrics or SIEM for alerts. For compliance (GDPR, PCI-DSS), logs must anonymize PII—use tokenization.
Example Workflow
-Picsart-CropImage.png)
This aligns with NIST's logging recommendations: Timely, sufficient, protected.
