AI-driven vulnerability detection and remediation workflows use machine learning and automation to identify, prioritize, and fix security issues in software systems.
These approaches analyze code, configurations, and runtime behavior to detect patterns associated with vulnerabilities more efficiently than manual methods.
By integrating AI into security workflows, organizations can accelerate detection, reduce false positives, and support faster remediation.
Core Concepts
AI-driven vulnerability detection scans code, dependencies, and runtime behavior for flaws like SQL injection or outdated libraries. Remediation workflows then generate fixes, such as code patches or dependency updates, integrating seamlessly into CI/CD pipelines.
This shift from reactive manual reviews to proactive automation aligns with industry standards like OWASP guidelines for secure AI practices.
-Picsart-CropImage.png)
Detection Techniques
AI enhances traditional scanning by learning patterns from vast datasets, spotting subtle issues like business logic flaws that rule-based tools miss. It processes code contextually, reducing noise and focusing on exploitable risks in hybrid cloud-native apps.
Detection starts with automated scans integrated into development tools. AI models, trained on CVE databases and real attacks, assign risk scores beyond CVSS, considering factors like asset criticality.
Popular AI Detection Methods:
1. Machine learning for anomaly detection in APIs and web apps (e.g., Acunetix).
2. Agentic AI scanners like Arnica for complex logic vulnerabilities.
3. Behavioral analysis in runtime, as in Traceable.ai for API threats.
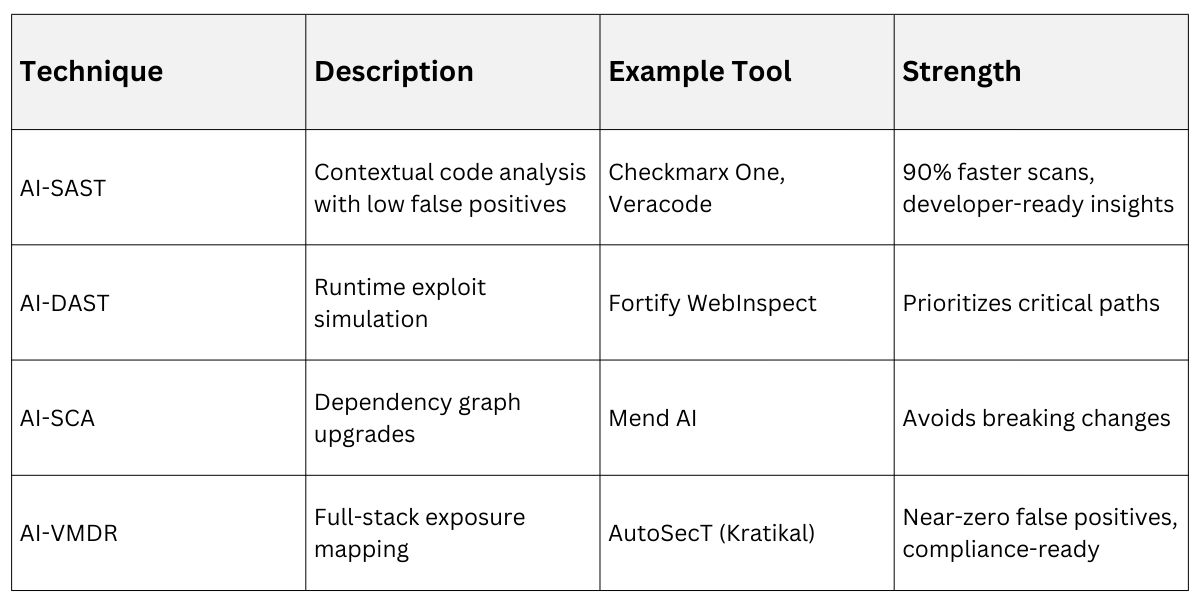
Practical Example: In a Python Flask app, AI-SAST detects an insecure deserialization flaw by analyzing data flows, flagging it high-risk if tied to user input.
Remediation Workflows
Remediation turns findings into action through AI-generated fixes pushed directly to pull requests. This closes the loop from detection to deployment, freeing teams for strategic work like threat modeling.
Steps for a Typical AI Workflow:
1. Scan and Triage: AI ingests results from SAST/SCA, filters high/critical issues, and ranks by exploitability (e.g., using exposure graphs).
2. Generate Fixes: AI analyzes code context to suggest patches—e.g., Mend AI proposes exact dependency versions or code snippets.
3. Validate and Apply: Auto-test fixes in a sandbox, then merge via CI/CD with human review for high-impact changes.
4. Verify and Monitor: Rescan post-fix, track MTTR, and use AI for continuous improvement via feedback loops.
Benefits in Practice:
1. Reduces developer time by 80% on fixes, as seen with Mend's ChatGPT-powered suggestions.
2. Handles SCA by mapping dependency trees to safe upgrades without breaks.
Example: For a Log4j vulnerability in a Java app, AI recommends pinning to a patched version and scans for transitive impacts.
 Benefits and Challenges
Benefits and Challenges
AI workflows boost efficiency, with tools like SentinelOne automating patches in test environments for near-instant fixes. They align with OWASP's AI security pillars: data protection, model integrity, and adversarial resilience.
Yet challenges persist, like ensuring AI suggestions don't introduce new flaws—always validate with human oversight.
Top Benefits
-Picsart-CropImage.png)
Common Challenges and Mitigations:
1. False fix suggestions: Use feedback loops to train models.
2. Integration silos: Choose tools with strong CI/CD support like Checkmarx.
3. Cost: Start with free tiers (e.g., open-source AI scanners).
Implementation Best Practices
Integrate AI early in the SDLC for "shift-left" security. Begin with pilot scans on critical repos, then expand.
Best Practices:
1. Adopt hybrid human-AI review: AI for 80% routine fixes, experts for edge cases.
2. Follow OWASP AI Guidance: Secure training data and monitor for prompt injection.
3. Use risk-based prioritization: over CVSS alone.
4. Monitor KPIs: Track fixed vulnerabilities/week and developer acceptance rates.
Example Rollout: Configure Mend in GitHub for auto-PR comments with fixes on SAST alerts, rescanning post-merge.
