Compliance standards such as GDPR and PCI-DSS define requirements for protecting sensitive data and ensuring responsible data handling practices.
GDPR focuses on personal data privacy and user rights, while PCI-DSS establishes security controls for handling payment card information.
Secure auditing supports these standards by providing traceability, accountability, and evidence that security controls are properly implemented and maintained.
GDPR: Protecting Personal Data Privacy
The General Data Protection Regulation (GDPR) is a comprehensive EU law enacted in 2018 to safeguard individuals' personal data across borders.
It applies to any app processing EU residents' data, emphasizing consent, transparency, and accountability—core to modern app security.
GDPR shifts power to users by mandating strict data handling rules. Non-compliance risks fines up to 4% of global annual revenue, pushing developers to embed privacy-by-design from the start.
Key Principles of GDPR
GDPR rests on seven foundational principles that guide app development. These ensure data is processed lawfully and securely, with practical implications for features like user sign-ups or analytics.
1. Lawfulness, Fairness, and Transparency: Always obtain explicit consent before collecting data. Example: An e-commerce app must clearly explain cookie usage, not bury it in fine print.
2. Purpose Limitation: Collect data only for specified reasons. Apps can't repurpose login info for unrelated marketing without fresh consent.
3. Data Minimization: Gather just enough data needed. Instead of storing full addresses, use postal codes for shipping.
4. Accuracy: Keep data up-to-date; implement easy correction tools in user profiles.
5. Storage Limitation: Delete data when no longer needed. Set auto-expiration for session logs after 30 days.
6. Integrity and Confidentiality: Protect against breaches using encryption and access controls.
7. Accountability: Document compliance with records of processing activities (ROPAs).
GDPR Compliance Steps for Developers
Follow this numbered process to integrate GDPR into your app's lifecycle, reducing breach risks.
1. Conduct a Data Audit: Map all personal data flows—e.g., identify where emails or IP addresses are stored in your database.
2. Appoint a Data Protection Officer (DPO): Required for large-scale processing; this role oversees compliance.
3. Implement Privacy by Design: Build consent banners and data export tools from day one.
4. Handle Data Subject Requests: Enable "right to be forgotten" via APIs for deletion within 30 days.
5. Perform DPIAs: Data Protection Impact Assessments for high-risk apps, like those using biometrics.
6. Report Breaches: Notify authorities within 72 hours if data is compromised.
7. Vendor Management: Ensure third-party services (e.g., cloud hosts) sign Data Processing Agreements (DPAs).
Pro Tip: Tools like OneTrust automate consent management, making compliance scalable for web apps.
PCI-DSS: Securing Cardholder Data
Payment Card Industry Data Security Standard (PCI-DSS) is a global standard for organizations handling credit card data, updated to version 4.0 in 2022 with enhanced multi-factor authentication (MFA) and continuous testing requirements.
It protects against fraud in payment-processing apps, mandatory for any app accepting cards.
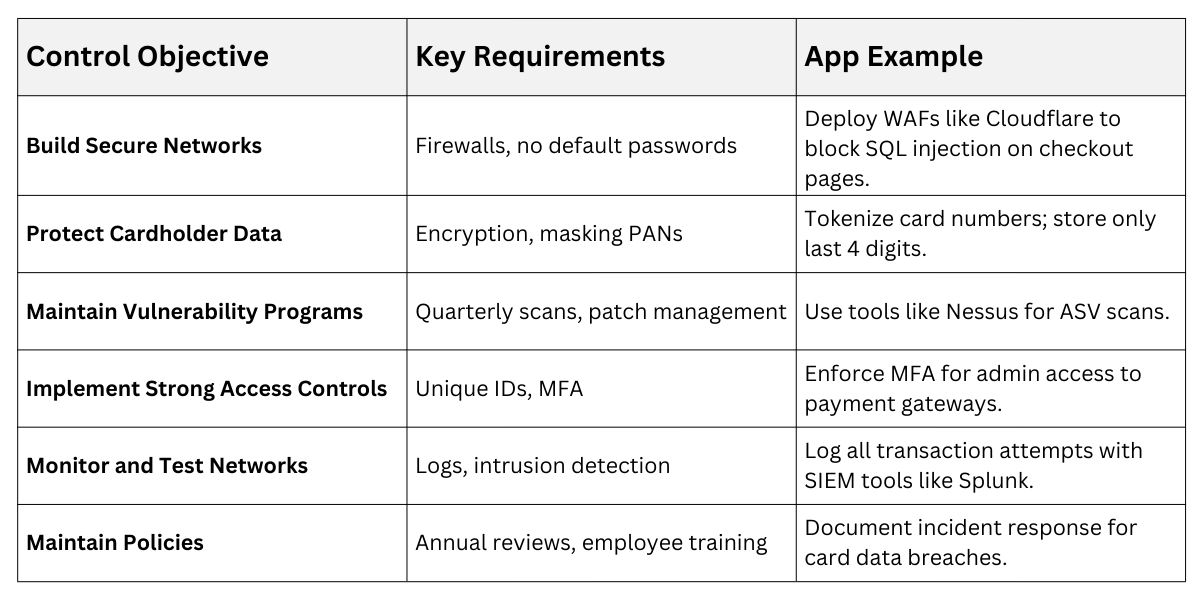
PCI-DSS comprises 12 core requirements grouped into six categories, focusing on secure networks, access, and monitoring. Compliance validates your app's payment flows, as seen in Stripe's PCI attestation boosting merchant trust.
Core PCI-DSS Requirements
Use this table to compare the six control objectives and their practical app impacts.
Achieving PCI-DSS Compliance
PCI levels vary by transaction volume (Level 1 for 6M+ transactions/year). Here's a streamlined path:
1. Scope Your Environment: Segment card data via VLANs to minimize the compliance footprint.
2. Pass Scans: Achieve quarterly external vulnerability scans (SAQ for smaller apps).
3. Self-Assess or Audit: Use SAQ forms or hire QSAs for Reports on Compliance (ROC).
4. Adopt New 4.0 Features: Enable targeted risk analyses (TRAs) by March 2025 for custom security controls.
5. Integrate with Code: Use PCI-compliant SDKs like Braintree to offload card storage.
Real-World Case: Target's 2013 breach of 40M cards stemmed from unsegmented networks—PCI-DSS now mandates this to prevent lateral movement.
Secure Auditing: Logging and Monitoring for Compliance
Secure auditing involves systematic logging, monitoring, and reviewing of app activities to detect anomalies and prove compliance with GDPR/PCI-DSS.
It provides the forensic trail regulators demand, with best practices evolving to include AI-driven anomaly detection per NIST SP 800-53 Rev 5 (2020).
Auditing turns reactive security into proactive defense, ensuring immutable logs for breach investigations. Tools like ELK Stack (Elasticsearch, Logstash, Kibana) make it feasible for devs.
Best Practices for Secure Auditing
Blend these techniques for robust, tamper-proof audits.
-Picsart-CropImage.png)
Auditing Process Workflow
Implement this numbered workflow for ongoing compliance.
1. Define Audit Scope: Align with regs—e.g., PCI Requirement 10 for logs.
2. Deploy Logging Agents: Integrate with app code (e.g., Python's logging module to Splunk).
3. Normalize and Centralize: Use SIEM for unified views across microservices.
4. Review and Report: Conduct monthly audits; automate with SOAR tools.
5. Test Integrity: Simulate breaches to verify log reliability.
6. Integrate with Incident Response: Link audits to playbooks for 72-hour GDPR reporting.
Example: A fintech app audits API calls, flagging a spike in PCI data exports as a potential insider threat.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
