Application Detection and Response techniques focus on identifying, investigating, and responding to security threats within applications.
ADR extends traditional monitoring by analyzing application behavior, logs, and telemetry to detect suspicious or malicious activity.
This approach helps security teams gain deeper visibility into application-level threats and respond quickly to incidents.
What is ADR?
Application Detection and Response (ADR) is a cybersecurity approach that monitors applications in real-time to detect and mitigate threats at the application layer.
Unlike traditional tools, it emphasizes behavioral analysis over perimeter defenses.
ADR emerged as the "EDR for apps," addressing gaps in endpoint and network security where application-specific attacks like API abuse thrive.
It integrates deeply into app environments via instrumentation, providing visibility into user interactions, data flows, and service communications.
Key Characteristics
1. Continuous monitoring: Tracks runtime behaviors to establish normal baselines.
2. Contextual insights: Correlates app data with threat intelligence for accurate alerts.
3. Automated actions: Blocks exploits or isolates issues without halting operations.
For example, consider an e-commerce app: ADR spots unusual API calls spiking database queries, flagging potential injection attempts before data loss occurs.
Core Components of ADR
ADR platforms rely on interconnected modules for end-to-end protection. These components work together to shift security left while enabling right-time responses in production.
-Picsart-CropImage.png)
Common Techniques include
1. Anomaly detection: Flags outliers, such as sudden privilege escalations.
2. Machine learning models: Statistical analysis predicts exploits like SQL injection or XSS.
3. Threat hunting: Proactive queries scan for indicators of compromise (IoCs).
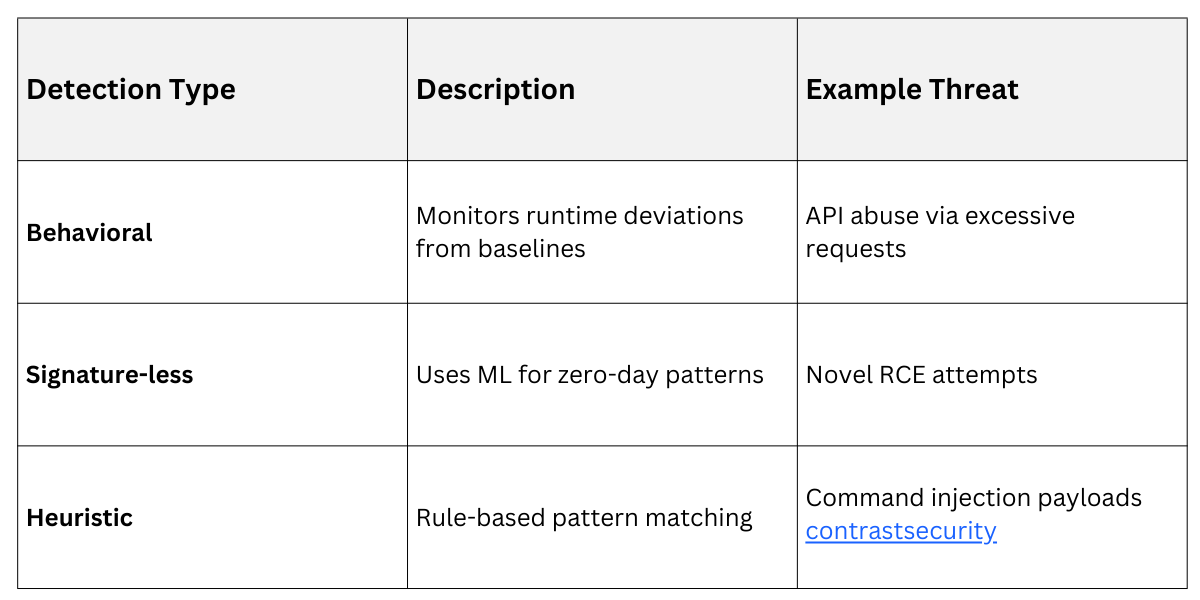
This table highlights why hybrid detection excels in dynamic cloud-native apps.
ADR Techniques in Action
ADR techniques operationalize detection into swift, effective responses. They emphasize automation and collaboration between DevSecOps teams.
Real-Time Threat Analysis
Once anomalies surface, ADR performs in-depth evaluation. It correlates events with known attack patterns, assigning severity scores for prioritization.
The process unfolds in these steps:
1. Ingestion: Aggregate app telemetry.
2. Analysis: Cross-reference with vulnerability databases like CVE.
3. Alerting: Generate contextual notifications with remediation guidance.
4. Triage: Prioritize based on business impact.
A Banking App Example: ADR detects anomalous session tokens, analyzes for token replay attacks, and alerts with exploit paths traced back to a rogue microservice.
Response and Remediation
Response capabilities distinguish ADR, enabling mean time to response (MTTR) under minutes. Solutions offer automated controls alongside manual options.
1. Blocking actions: Quarantine malicious requests at the app layer.
2. Rollback features: Revert compromised states without full restarts.
3. Policy enforcement: Dynamically tighten access controls.
Best practices include testing responses in staging to avoid disruptions, aligning with DevSecOps pipelines.
ADR vs. Traditional AppSec
ADR addresses limitations of legacy tools like WAFs and SAST/DAST. Here's a structured comparison for clarity.
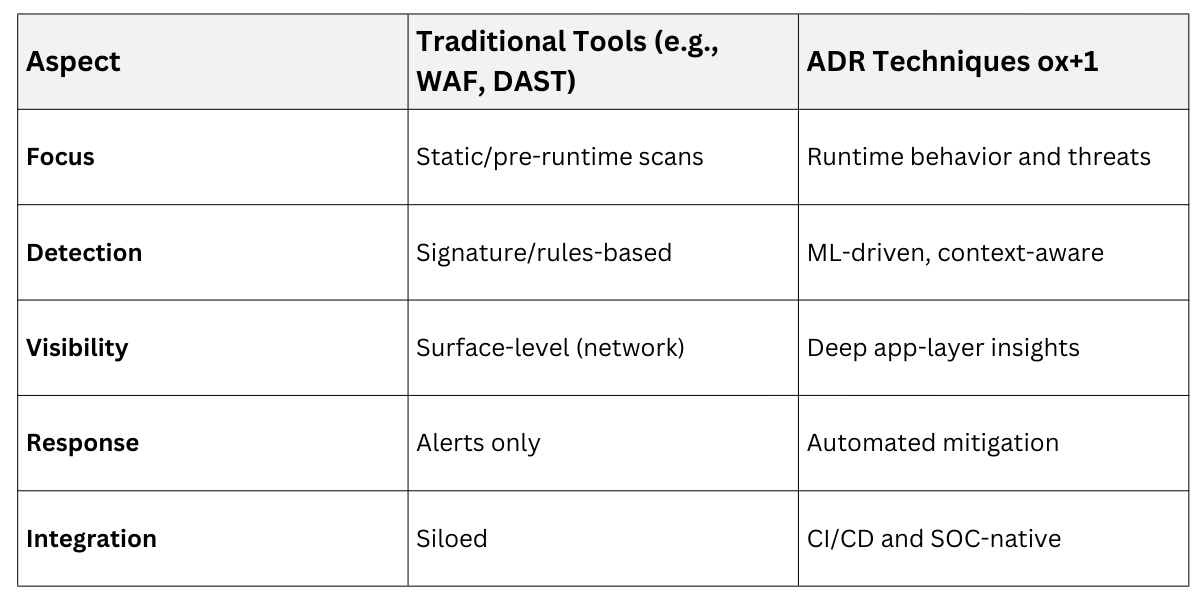
WAFs block known patterns but miss zero-days; ADR adapts via learning, reducing false positives by 50-70% in mature setups.
Implementing ADR in Your Environment
Practical rollout starts with assessment and scales to full adoption. Focus on tools supporting compliance like GDPR or PCI-DSS.
Selection Criteria
Choose platforms with:
1. Threat intelligence integration: Enriches alerts with global data.
2. Scalability: Handles containerized/Kubernetes workloads.
3. Low overhead: Non-intrusive instrumentation (<5% perf impact).
Vendors like OX Security or Contrast emphasize developer-friendly dashboards.
Deployment Steps
1. Pilot in non-prod: Instrument critical apps.
2. Baseline tuning: Refine models over 2-4 weeks.
3. Integrate pipelines: Embed in CI/CD for shift-left.
4. Train teams: Run tabletop exercises for response.
Example: A SaaS provider deploys ADR in Kubernetes, catching a deserialization flaw during Black Friday traffic spikes.
Benefits and Challenges
ADR delivers measurable gains but requires cultural shifts. Benefits include reduced attack surface and faster remediation.
1. Proactive security: Surfaces issues pre-production.
2. Collaboration boost: Bridges AppSec-Dev gaps.
3. Adaptability: Evolves with threats via ML.
Challenges
1. Skill gaps: Needs expertise in app telemetry.
2. False positives: Initial tuning phase critical.
3. Cost: Enterprise tools start at $50K/year.
Mitigate by starting small and leveraging managed services.
