The CIA triad represents the foundational principles of information security that guide the design and protection of systems and data.
Confidentiality focuses on preventing unauthorized access to sensitive information, integrity ensures that data remains accurate and unaltered, and availability guarantees that systems and data are accessible to authorized users when needed.
What is the CIA Triad?
The CIA triad is a classic model in cybersecurity that outlines three core principles for securing data and systems.
Developed in the 1970s and refined by standards like NIST, it provides a balanced checklist for security professionals.
Think of it as the "three legs of a stool"—if one wobbles, the whole thing topples. In application security, we apply it to protect user data, APIs, and backend services against modern threats like ransomware and DDoS attacks.
Origins and Evolution
The triad emerged from early U.S. military needs but has evolved with digital tech. Today, NIST SP 800-53 (Rev. 5) and ISO 27001 integrate it as a benchmark for compliance.
1. Historical roots: Born from the "secure computing" era, formalized in the 1980s.
2. Modern adaptations: Extended models like CIANA (adding Non-repudiation and Authentication) appear in cloud-native apps, but CIA remains the core.
This evolution underscores its timeless relevance—it's not theory; it's the blueprint for tools like encryption libraries in Python's cryptography module.
Confidentiality: Protecting Data Privacy
Confidentiality ensures that sensitive information is accessible only to authorized users, preventing unauthorized disclosure. In apps, this means shielding data like passwords, health records, or payment details from prying eyes.
Breaches here often make headlines, but simple controls can stop them. Let's break it down with practical steps and examples relevant to web development.
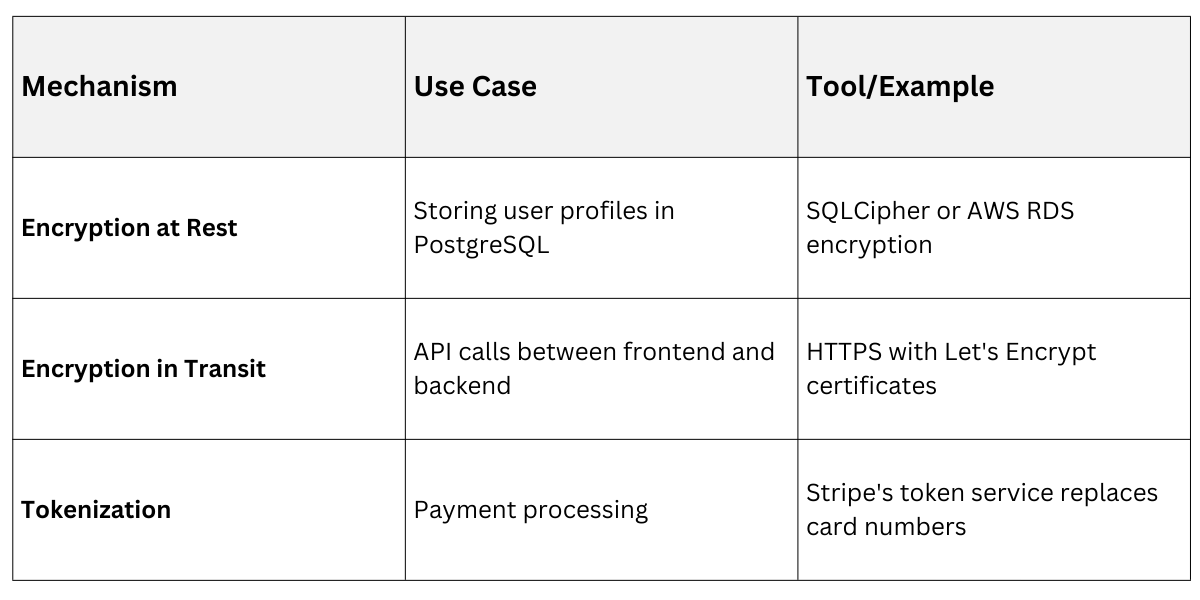
Key Mechanisms for Confidentiality
Developers implement confidentiality through layered defenses. Here's how:
1. Encryption: Convert data into unreadable code. Use AES-256 for data at rest (e.g., database fields) and TLS 1.3 for data in transit (standard since 2025 for HTTPS).
2. Access Controls: Role-based access control (RBAC) limits who sees what—think JWT tokens in FastAPI apps.
3. Data Masking: Hide sensitive parts, like showing only the last four digits of a credit card.
Practical Example: In a Django e-commerce app, encrypt customer emails in the database. Without it, a SQL injection could expose millions—Equifax's 147 million record leak started this way.
Common Threats and Mitigations
Threats like eavesdropping (man-in-the-middle) target confidentiality. Mitigate with:
.png)
By prioritizing confidentiality, your apps comply with GDPR or India's DPDP Act 2023, building user trust.
Integrity: Ensuring Data Trustworthiness
Integrity guarantees that data remains accurate, complete, and unaltered except by authorized means. It's about detecting and preventing tampering, so users can rely on your app's outputs.
In application security, integrity failures lead to disasters like manipulated votes or falsified bank balances. Robust checks make your code tamper-proof.
Techniques to Maintain Integrity
Follow these numbered steps for implementation:
1. Hashing: Use SHA-256 to create a unique "fingerprint" of data. Store hashes, not originals—verify changes by re-hashing.
2. Digital Signatures: Pair hashes with public-key crypto (e.g., ECDSA) to prove authenticity.
3. Input Validation: Sanitize all user inputs to block injection attacks.
Benefits in Web Apps
1. Prevents silent alterations in REST APIs.
2. Ensures firmware updates aren't hijacked (critical for IoT apps).
3. Supports blockchain-like immutability in logs.

Practical Example: A Python ML model serving predictions via FastAPI. Hash inputs/outputs; if a hacker tweaks data mid-flight, the mismatch flags it—vital for financial fraud detection apps.
Best Practices from Standards
Per OWASP Top 10 (2025), checksums and message authentication codes (MACs) are non-negotiable. Audit integrity in CI/CD pipelines to catch issues early.
Availability: Keeping Systems Accessible
Availability ensures authorized users can access systems and data when needed, without undue interruptions. Downtime costs businesses millions—think of it as your app's "uptime promise."
Strategies for High Availability
Build redundancy into your architecture:
1. Load Balancing: Distribute traffic across servers (e.g., NGINX or AWS ELB).
2. Redundancy: Use multi-region deployments to survive outages.
3. DDoS Protection: Rate-limit and filter traffic.

Practical Example: During Black Friday, a retail app faces DDoS. Cloudflare's 2025 WAF scrubs attacks, keeping checkout available—mirroring the 2023 Optus outage that cost $1M/hour.
Emerging Threats and Defenses
Ransomware and API abuse surged in 2025 (per Verizon DBIR). Counter with:
1. Rate Limiting: Cap requests per IP (e.g., 100/min in Express.js).
2. Backup and Recovery: RPO/RTO under 4 hours, per NIST.
Balancing the CIA Triad in Practice
No principle stands alone—trade-offs exist. Over-encrypting hurts availability; skimping on integrity risks confidentiality.
Real-World Application
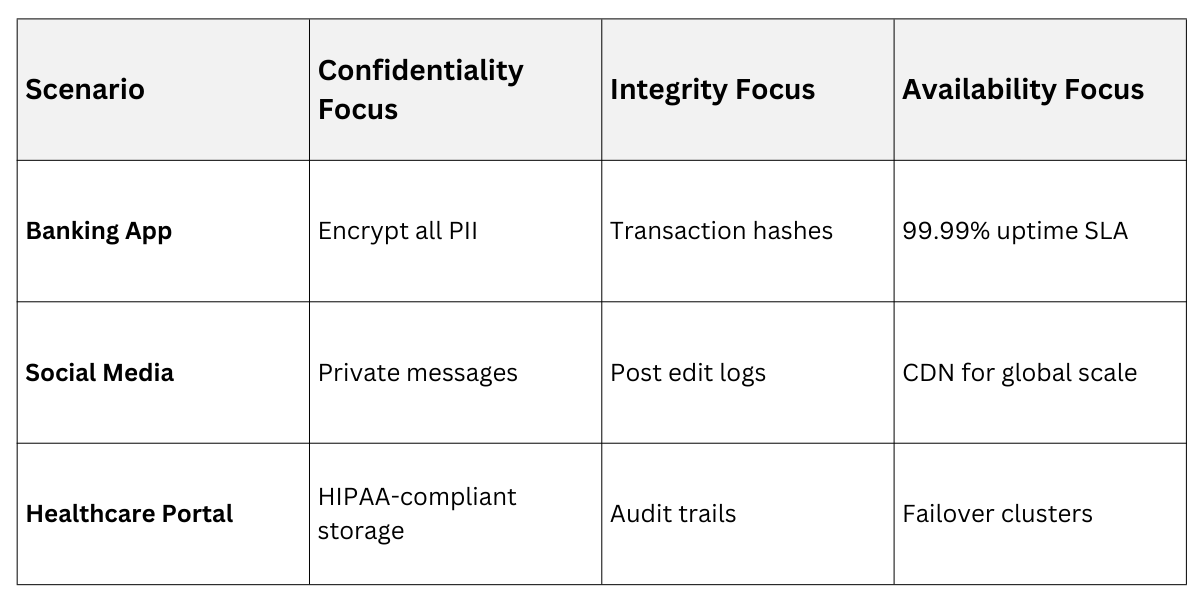
In code reviews, score features against CIA: Does this endpoint leak data? Can it be spoofed? Will it crash under load? Tools like SonarQube automate this.
Developer Tip: Integrate CIA into Agile sprints—tag user stories with triad impacts for holistic security.
