Secure HTTP headers and API security fundamentals play a key role in protecting web applications and services from common attacks.
Secure HTTP headers instruct browsers on how to handle content, connections, and data, helping to prevent issues such as cross-site scripting, clickjacking, and insecure transport.
API security fundamentals focus on safeguarding APIs through proper authentication, authorization, input validation, and rate limiting.
Secure HTTP Headers: The Basics
Secure HTTP headers are key-value pairs in HTTP responses that enhance security by controlling client behavior, mitigating risks like injection attacks and session hijacking.
They don't encrypt data but enforce policies that browsers and proxies must follow, making them a lightweight yet powerful layer in your app's defense stack.
Why Headers Matter in Modern Web Apps
Without proper headers, attackers exploit default browser leniency. For instance, a missing Content-Security-Policy (CSP) header lets malicious scripts run, enabling XSS.
1. Universal applicability: Work across HTTP/1.1, HTTP/2, and HTTP/3 (QUIC).
2. No code changes needed: Set them server-side via middleware.
3. Compliance boost: Aligns with GDPR, PCI-DSS, and NIST SP 800-53.
Practical Example: In a FastAPI app, add headers like this
from fastapi import FastAPI, Response
app = FastAPI()
@app.get("/")
def read_root(response: Response):
response.headers["X-Content-Type-Options"] = "nosniff"
return {"message": "Secure response"}Essential Secure HTTP Headers
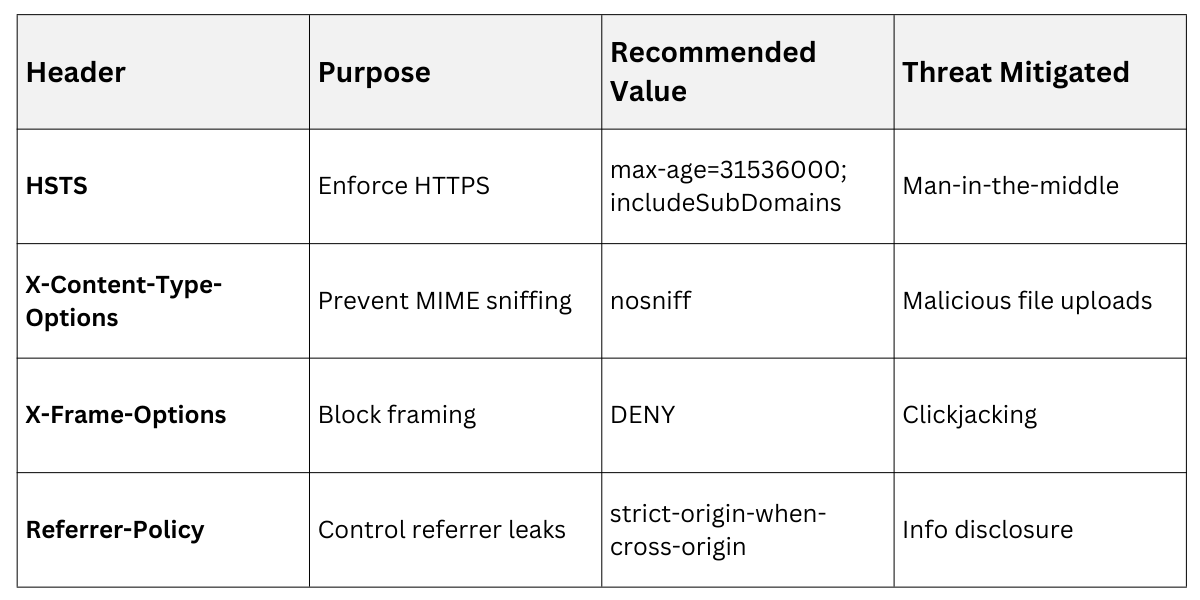
These headers form the core of a security baseline. OWASP recommends enabling at least six for production apps. Here's a breakdown of the must-haves, with setup steps and rationale.
Core Defensive Headers
Each header targets a specific threat vector. Implement them progressively to avoid breaking legacy clients.
1. Strict-Transport-Security (HSTS): Forces HTTPS-only traffic.
Syntax: Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
max-age: Seconds until expiration (1 year ideal).
Example: Prevents downgrade attacks on login pages.
2. X-Content-Type-Options: nosniff: Blocks MIME-type sniffing.
Stops browsers from executing uploaded files as scripts.
3. X-Frame-Options: DENY (or CSP frame-ancestors): Prevents clickjacking.
DENY: No framing at all; SAMEORIGIN: Only same-site iframes.
 Advanced Headers for Content and Permissions
Advanced Headers for Content and Permissions
Build on basics with these for finer control.
1. Content-Security-Policy (CSP): Defines allowed sources for scripts, styles, etc.
Example: Content-Security-Policy: default-src 'self'; script-src 'self' https://trusted.cdn.com
Benefits: Reduces XSS by 70% per OWASP tests.
Tip: Start with report-only mode to test.
2. Permissions-Policy: Replaces Feature-Policy (deprecated in 2023).
Limits features like geolocation: Permissions-Policy: geolocation=(), camera=()
3. Cross-Origin-Embedder-Policy (COEP) and Cross-Origin-Opener-Policy (COOP): Enable cross-origin isolation for Spectre/Meltdown mitigations (Chrome 2024+ enforcement).
Popular Frameworks
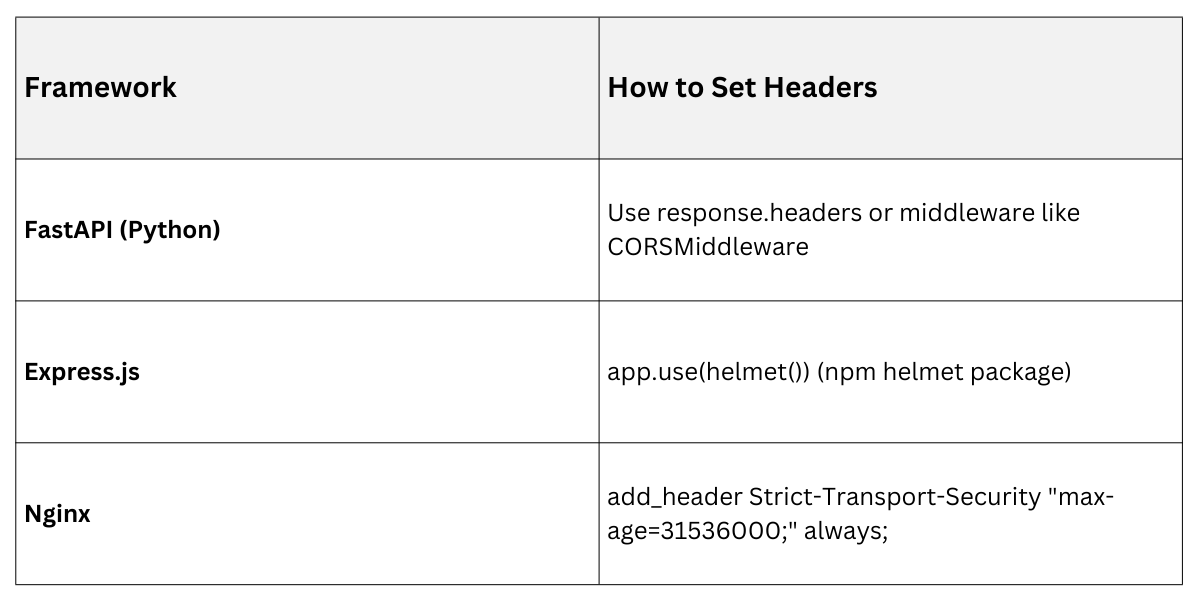 API Security Fundamentals
API Security Fundamentals
APIs power modern apps, from mobile backends to microservices, but expose endpoints to unauthorized access if unsecured. Fundamentals focus on authentication, rate limiting, and input validation, per OWASP API Security Top 10 (2023 update).
Key Principles for API Protection
Secure APIs treat every request as potentially hostile. Start with the "zero trust" model: authenticate, authorize, and validate relentlessly.
Essentials
.png)
Real-World Pitfall: The 2025 Twilio breach stemmed from weak API keys—always rotate and scope them.
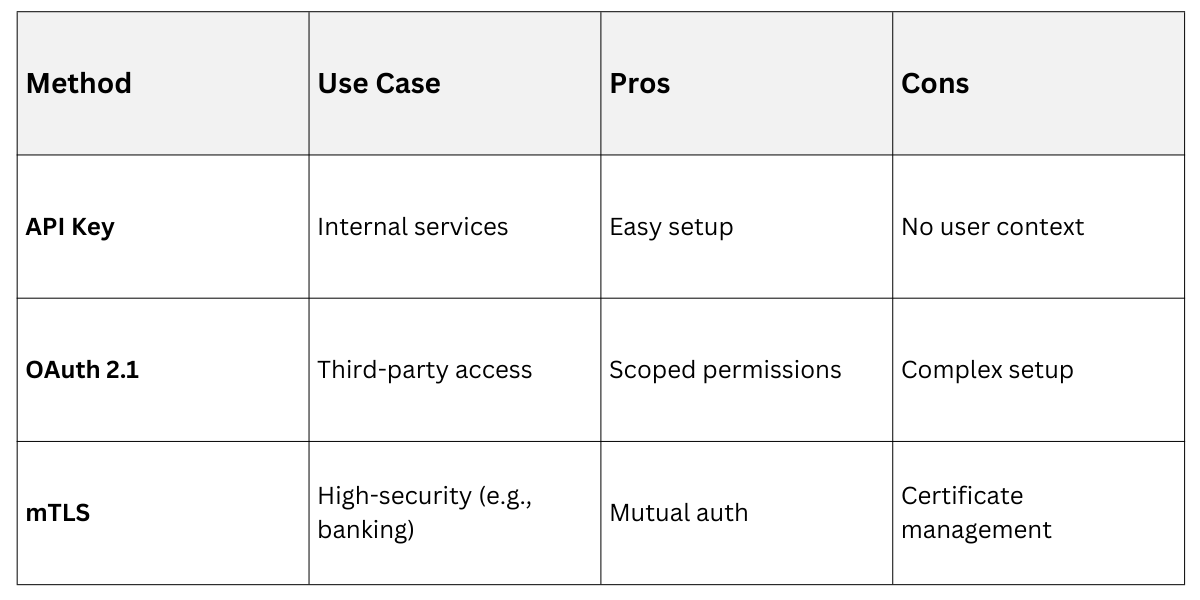
Authentication and Authorization in APIs
Protect endpoints with layered auth. Avoid basic auth; it's crackable in seconds.
1. API Keys: Simple for server-to-server; store in headers like X-API-Key.
2. OAuth 2.1 / OpenID Connect: Token-based for users (RFC 9068, 2024 updates).
Flow: Client requests token → Server validates JWT signature.
3. JWT Best Practices:
Short expiry (15 mins).
RS256 signing (not HS256).
Validate claims: iss, aud, exp.
Comparison of Auth Methods
Example FastAPI JWT endpoint
from fastapi import Depends, HTTPException
from fastapi.security import HTTPBearer
security = HTTPBearer()
def verify_token(token: str = Depends(security)):
# Decode and validate JWT
if not is_valid_jwt(token.credentials): # Custom func
raise HTTPException(401, "Invalid token")
return tokenRate Limiting, Validation, and Monitoring
Prevent abuse and ensure data integrity.
Rate Limiting Steps (using Redis in Python):
1. Track requests per IP/user in Redis (e.g., INCR ip:{ip}:requests).
2. Set window (e.g., 100 reqs/hour).
3. Reject with 429 Too Many Requests.
Input Validation: Use schemas (Pydantic in FastAPI) to reject malformed JSON.
CORS: Access-Control-Allow-Origin only for trusted domains.
Monitoring: Log all 4xx/5xx with tools like ELK stack.
OWASP API Top 10 Threats and Counters
1. Broken auth → JWT + scopes.
2. Excessive data exposure → Pagination and field selection.
3. Mass assignment → Whitelist inputs.
Integrating Headers and API Security
Combine them holistically. For a REST API:
1. Apply headers to all responses.
2. Use API gateways (e.g., Kong, AWS API Gateway) for centralized enforcement.
3. Test with tools: OWASP ZAP or Burp Suite.
Deployment Checklist
1. Audit current headers (curl -I yourapi.com).
2. Enable in staging.
3. Monitor for breakage.
4. Submit HSTS preload list (hstspreload.org).
