Container and cloud-native application security focuses on protecting applications that are built, deployed, and run using containers and cloud-native technologies.
These environments introduce new security challenges related to shared infrastructure, dynamic workloads, and complex orchestration platforms.
Effective security practices address risks across the entire lifecycle, from container image creation to runtime monitoring in production.
Core Concepts in Container Security
Containers package apps with their dependencies for portability, but this speed comes with risks if security isn't baked in from the start.
Containers rely on isolation via kernel features like namespaces and cgroups, yet a single vulnerability can compromise the host.
Image security is paramount, as images often pull from public registries with unpatched flaws.
-Picsart-CropImage.png)
Key Stats highlight the urgency: In 2025, Sysdig reported 60% of production images had high-severity vulnerabilities.
Scanning and Hardening Images: Start by treating images as untrusted code. Use tools like Trivy or Clair for pre-build scans, integrating them into CI/CD.
Follow these Steps to Harden Images:
1. Choose minimal bases like distroless or Wolfi OS, which strip unnecessary binaries.
2. Scan with docker scout (Docker's built-in) or Anchore: trivy image myapp:latest.
3. Remove setuid binaries and unnecessary packages: Edit your Dockerfile to RUN apt-get purge -y sudo.
4. Sign images with cosign or Docker Content Trust for tamper-proofing.
5. Use multi-stage builds to shrink attack surface: Copy only runtime artifacts.

Practical Example: In a Python Flask app container, scan revealed log4j-like issues in dependencies—fixed by pinning requirements.txt versions.
Runtime Security in Container Environments
Once deployed, containers face runtime threats like privilege escalation or side-channel attacks. Runtime security monitors behavior post-deployment, enforcing policies dynamically.
Orchestrators like Kubernetes amplify risks through pod scheduling on shared nodes. Tools like Falco detect anomalies via syscalls.
Implementing Pod Security Standards
Kubernetes introduced Pod Security Standards (PSS) in v1.25 (enhanced in 1.30), replacing deprecated policies. Apply them via admission controllers.
PSS Profiles Comparison

Enforce via securityContext
apiVersion: v1
kind: Pod
spec:
securityContext:
runAsNonRoot: true
seccompProfile:
type: RuntimeDefaultExample: A Node.js microservice pod using restricted PSS prevents container escapes seen in 2024 breaches.
Cloud-Native Security Layers
Cloud-native apps leverage service meshes, serverless, and GitOps, demanding layered defenses. Think of it as a zero-trust model: verify everything, assume breach.
CNCF's security landscape (2025 update) emphasizes shift-left—secure early in the pipeline.
Service Mesh and Network Policies
Service meshes like Istio or Linkerd encrypt traffic and enforce mTLS automatically. They prevent east-west attacks in Kubernetes clusters.
-Picsart-CropImage.png)
Practical Tip: In a e-commerce app, Istio's telemetry caught a pod injecting malicious traffic, blocking it via policy.
Common Network Policy Example
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
spec:
podSelector: { matchLabels: { app: frontend } }
policyTypes: [ Ingress ]
ingress:
- from: [ { podSelector: { matchLabels: { app: backend } } } ]Securing CI/CD Pipelines and Secrets
Vulnerable pipelines are a top attack vector—2025 Verizon DBIR noted 40% of breaches started here. Secrets management prevents leaks.
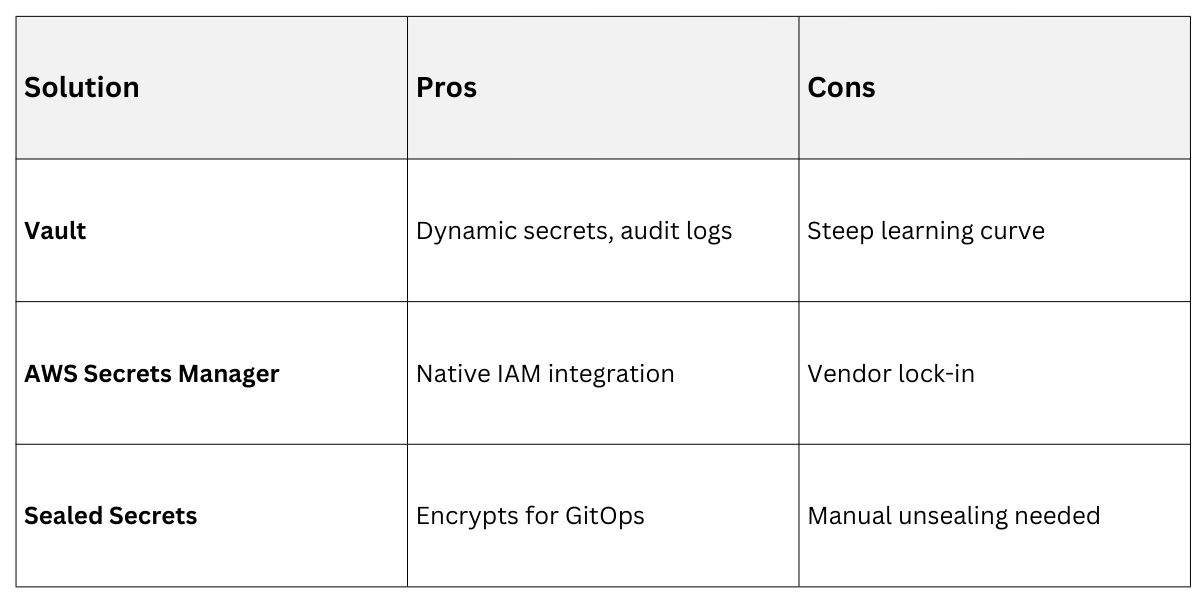
Use External Secrets Operator over Kubernetes secrets, pulling from HashiCorp Vault or AWS Secrets Manager.
Pipeline Best Practices
Integrate security gates:
1. SLSA (Supply-chain Levels for Software Artifacts) framework verifies build integrity.
2. Sign commits and artifacts with sigstore/cosign.
3. Use OPA Gatekeeper for policy-as-code: Reject images without signatures.
Example pipeline (GitHub Actions snippet)
- name: Scan Image
uses: aquasecurity/trivy-action@master
with:
image-ref: 'myregistry/app:${{ github.sha }}'
severity: 'CRITICAL,HIGH'Secrets Management Options
 Threat Modeling and Compliance
Threat Modeling and Compliance
Tailor security to your app: Model threats using STRIDE (Spoofing, Tampering, etc.) adapted for containers.
Reference NIST SP 800-190 for container-specific controls.
Runtime: eBPF tools like Tetragon for kernel-level monitoring.
Compliance: SOC 2 via tools like Prisma Cloud.
Real-World: A 2025 Capital One-like breach exploited unpatched container hosts—mitigated by auto-updating via Flux GitOps.
