Secure software development lifecycle integration involves embedding security practices into every phase of the software development process, from requirements and design to implementation, testing, deployment, and maintenance.
Rather than treating security as a separate or final step, this approach ensures that potential risks are identified and addressed early.
By integrating security activities throughout the lifecycle, organizations can reduce vulnerabilities, lower remediation costs, and build more resilient software systems.
Why Integrate Security in SDLC?
Traditional SDLC focuses on functionality and speed, often treating security as an afterthought, which leads to costly fixes in production.
Shifting security left—introducing it early—catches issues when they're cheapest to resolve.
Organizations face rising threats like supply chain attacks and zero-days, making SSDLC critical for compliance and trust. Benefits include fewer vulnerabilities, faster releases, and cultural buy-in across DevOps teams.
Traditional vs Secure SDLC
The classic SDLC model risks bolting on security late, while SSDLC weaves it in proactively.
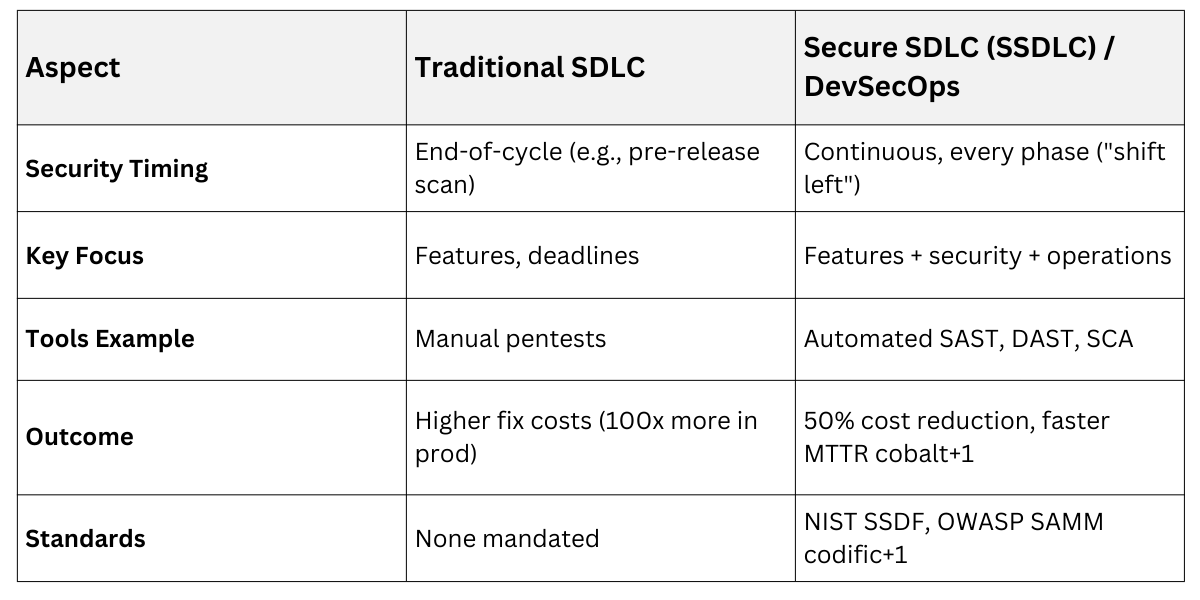
This table highlights how SSDLC transforms silos into collaboration.
Key Industry Standards
Standards provide blueprints for SSDLC implementation, adaptable to Agile or Waterfall.
NIST Secure Software Development Framework (SSDF) defines four pillars: Prepare Organization (PO), Protect Software (PW), Produce Well-Secured Software (PS), and Respond to Vulnerabilities (RV).
It mandates tasks like defining security roles (PO.1) and vulnerability prioritization (RV.2), with U.S. federal compliance via OMB M-22-18.
OWASP SAMM assesses maturity across Governance, Design, Implementation, Verification, and Operations, using risk-driven streams for tailored roadmaps. Both emphasize training, automation, and metrics like mean time to remediate (MTTR).
SSDLC Phases and Integration Practices
SSDLC maps security to standard phases: Requirements, Design, Implementation, Verification, Deployment, and Maintenance. Each includes automated gates in CI/CD pipelines.
Follow these numbered steps for phase-by-phase integration:
-Picsart-CropImage.png)
This ensures no phase skips security.
1. Requirements Phase: Start with security by defining threat profiles and compliance needs, avoiding vague specs that invite flaws.
Document abuse cases (e.g., unauthorized access attempts) next to user stories.
Include standards like GDPR data minimization or PCI-DSS controls.
Use tools like threat modeling templates from OWASP.
Example: For a banking app, require multi-factor authentication (MFA) from the outset, preventing later rewrites.
2. Design Phase: Threat modeling visualizes attacks, prioritizing defenses like defense in depth.
Apply Zero Trust: Verify every access.
Design secure APIs with rate limiting.
Review for supply chain risks, like third-party libs.
Practical Example: In e-commerce design, segment user data flows to limit breach impact.
3. Implementation Phase: Code with security baked in via training and linters, reducing injection flaws by 90%.
Developers use secure coding guidelines, scanning commits automatically.
1. Integrate SAST (Static Application Security Testing) tools like Semgrep for early flaw detection.
2. Scan dependencies with SCA (Software Composition Analysis) for known vulns.
3. Generate SBOMs (Software Bill of Materials) for transparency.
Example: Parameterize SQL queries to block injection: cursor.execute("SELECT * FROM users WHERE id = ?", (user_id,)) instead of string concatenation.
4. Verification Phase
Test rigorously with automated and manual methods to validate controls.
Shift-left testing runs in CI/CD, catching 70% more issues pre-merge.
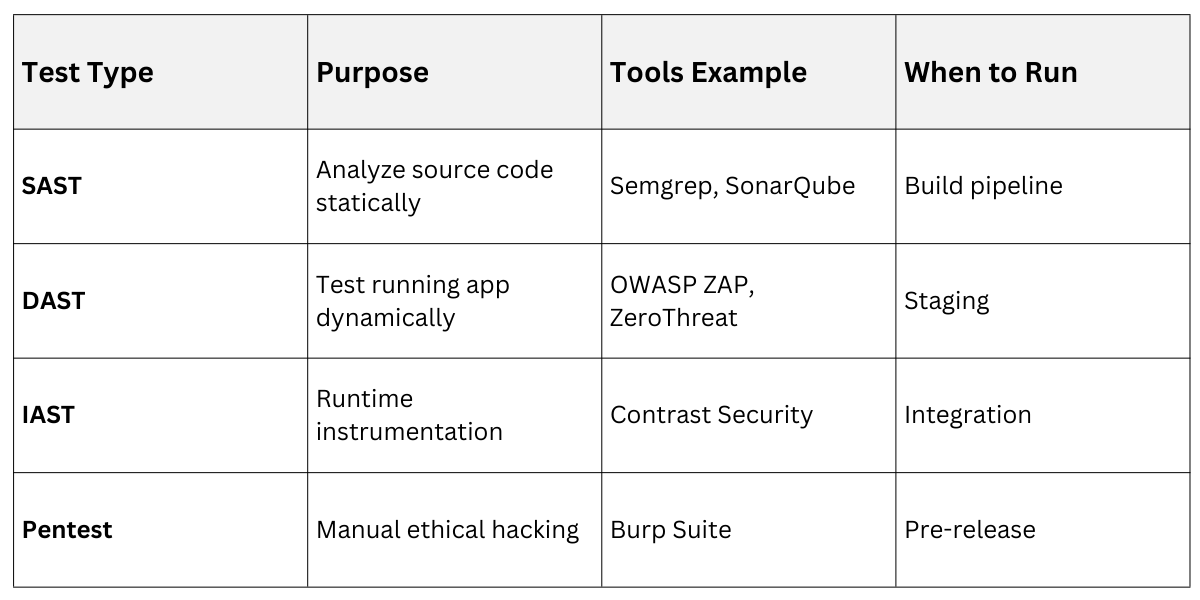
Include fuzzing for edge cases and SCA for open-source risks.
Deployment and Maintenance
Deploy securely with immutable infrastructure and monitor continuously.
1. Use IaC (Infrastructure as Code): scans (e.g., Terraform with Checkov).
2. Implement SLSA (Supply-chain Levels for Software Artifacts): for provenance and signing.
3. Post-deploy: Runtime monitoring, patch management, and incident response.
Example: Kubernetes clusters with network policies block lateral movement. Track metrics like vulnerability age via dashboards.
Tools and DevSecOps Practices
DevSecOps automates SSDLC with pipeline gates, embracing AI for smarter scans.
-Picsart-CropImage.png)
Best Practices: Policy-as-code, immutable builds, and shared responsibility training
